Linux for digital machine units the stage for this enthralling narrative, providing readers a glimpse right into a story that’s wealthy intimately with informal stylish fashion and brimming with originality from the outset. As we embark on this journey, we are going to delve into the world of Linux digital machines, exploring the kinds, configurations, administration, and safety of those digital entities.
The idea of digital machines has revolutionized the way in which we work together with computing programs, offering a versatile and scalable answer for numerous functions, from improvement to manufacturing environments. Linux, with its huge array of distributions and customization choices, has emerged because the premier selection for digital machine infrastructure.
Varieties of Linux Digital Machines: Linux For Digital Machine
Linux digital machines have grow to be a necessary device for builders, testers, and directors. They provide an economical and versatile method to run a number of working programs on a single host machine. On this part, we are going to discover the various kinds of Linux digital machines and their options.
These virtualization options have gained reputation attributable to their capacity to run a number of OS situations on a single bodily machine. This flexibility permits customers to check, develop, and deploy functions with better ease.
Virtualization Options
There are a number of virtualization options out there for Linux digital machines. Every answer has its personal set of options, benefits, and limitations.
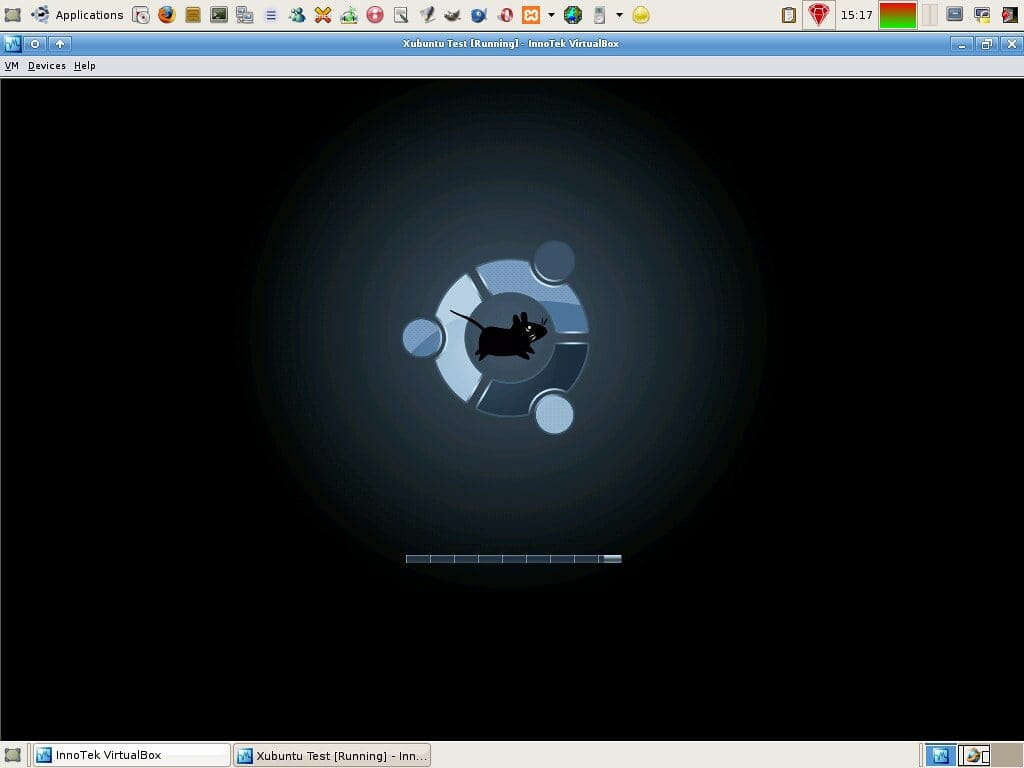
VirtualBox
VirtualBox is a well-liked open-source virtualization answer developed by Oracle. It helps a variety of working programs, together with Linux, Home windows, and macOS. VirtualBox gives a user-friendly interface and gives superior options similar to snapshotting, cloning, and digital networking.
A number of the key options of VirtualBox embrace:
- Assist for a number of working programs: VirtualBox can run a number of OS situations on a single host machine.
- Snapshotting and cloning: VirtualBox permits customers to create snapshots of their VMs and clone them to create new VMs.
- Digital networking: VirtualBox gives assist for digital networking, which permits customers to create and handle digital networks.
- Multiplatform assist: VirtualBox is obtainable for Home windows, macOS, and Linux host working programs.
- Intensive documentation: VirtualBox gives in depth documentation and a big neighborhood of customers and builders.
VirtualBox is a well-liked selection amongst builders and directors attributable to its user-friendly interface and superior options.
VMware
VMware is a industrial virtualization answer that gives a variety of options and instruments. It helps a number of working programs and gives superior options similar to snapshotting, cloning, and digital networking.
A number of the key options of VMware embrace:
- Assist for a number of working programs: VMware can run a number of OS situations on a single host machine.
- Snapshotting and cloning: VMware permits customers to create snapshots of their VMs and clone them to create new VMs.
- Digital networking: VMware gives assist for digital networking, which permits customers to create and handle digital networks.
- Multiplatform assist: VMware is obtainable for Home windows, macOS, and Linux host working programs.
- Enhanced safety features: VMware gives enhanced safety features, together with encryption and entry controls.
VMware is a well-liked selection amongst companies attributable to its superior options and strong instruments.
KVM (Kernel-based Digital Machine), Linux for digital machine
KVM is an open-source virtualization answer that gives high-performance virtualization capabilities. It helps a number of working programs and gives options similar to snapshotting, cloning, and digital networking.
A number of the key options of KVM embrace:
- Excessive-performance virtualization: KVM gives high-performance virtualization capabilities, making it appropriate for demanding workloads.
- Snapshotting and cloning: KVM permits customers to create snapshots of their VMs and clone them to create new VMs.
- Digital networking: KVM gives assist for digital networking, which permits customers to create and handle digital networks.
- Multiplatform assist: KVM is obtainable for Linux host working programs.
- Low overhead: KVM has a low overhead in comparison with different virtualization options.
KVM is a well-liked selection amongst Linux directors attributable to its high-performance capabilities and low overhead.
Every virtualization answer has its personal strengths and weaknesses, and the selection finally is determined by the particular wants of the person.
Putting in Linux on a Digital Machine
Putting in Linux on a digital machine gives a handy and risk-free surroundings to discover and study Linux with out affecting the host machine’s working system. This methodology is right for testing, improvement, and coaching functions. With the fitting virtualization software program and an acceptable Linux distribution, you may create a digital machine with a totally purposeful Linux surroundings.
Choosing the Appropriate Set up Medium
The set up medium determines how you’ll set up Linux in your digital machine. You’ve gotten two choices: CD/DVD or ISO file.
The ISO file is a digital copy of a CD/DVD that can be utilized to put in Linux.
To put in Linux from a CD/DVD, that you must create a digital CD/DVD drive in your digital machine settings. To make use of an ISO file, you may connect it to the digital machine as a CD/DVD system after which observe the set up course of from the ISO file.
- Use a CD/DVD drive in case you desire to have a bodily set up media or in case your digital machine software program doesn’t assist ISO information.
- Select an ISO file in case you desire to have a digital set up media or if you wish to keep away from the trouble of burning a CD/DVD.
- Obtain a Linux ISO file from a good supply, such because the official Linux distribution web site.
Configuring Digital Machine Settings
To run Linux on a digital machine, that you must configure the digital machine settings, together with CPU, reminiscence, and community.
Correctly configuring these settings ensures optimum efficiency and a easy person expertise.
To configure the digital machine settings:
- Assign a minimal of two GB of RAM and a couple of CPU cores to the digital machine.
- Be sure that the digital machine has entry to a community, both by means of a bridge community or a digital community interface.
- Configure the digital machine to make use of an acceptable CPU structure, similar to 64-bit or 32-bit, relying on the Linux distribution you might be utilizing.
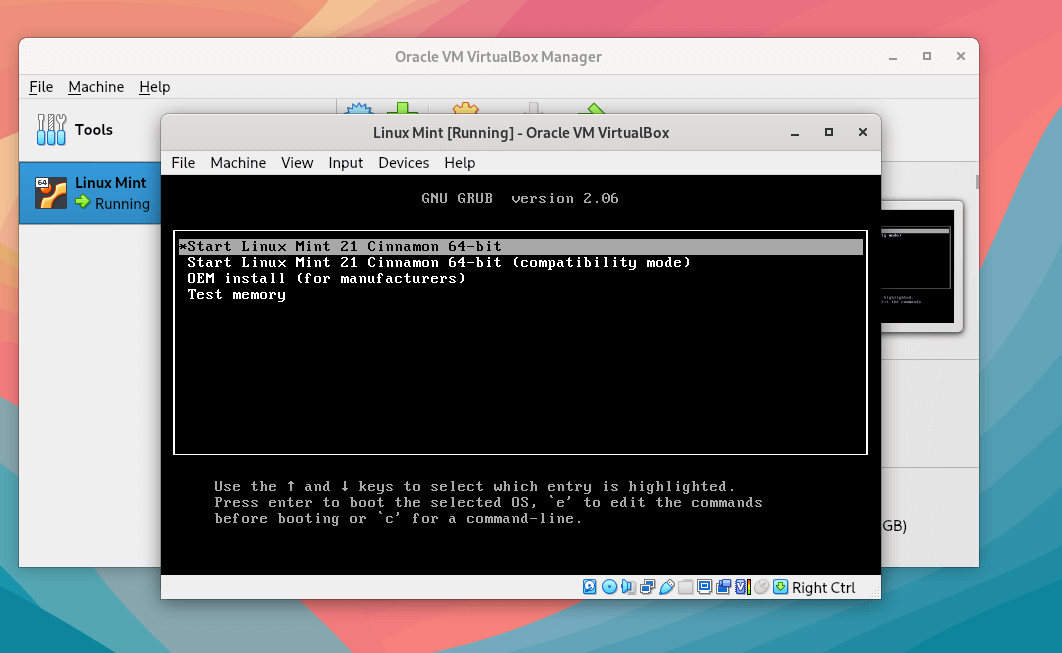
Putting in Linux on the Digital Machine
Upon getting chosen the right set up medium and configured the digital machine settings, you can begin the set up course of. Observe the set up wizard to put in Linux on the digital machine.
- Begin the digital machine and boot from the set up media.
- Observe the set up wizard to pick out the language, keyboard structure, and time zone.
- Choose the partition scheme and set up Linux on the digital machine.
- Configure the community and different settings as wanted.
- Begin the digital machine and login to your new Linux surroundings.
Configuring Linux Digital Machines
Configuring Linux digital machines is a vital step in making certain they run easily and effectively. It entails organising numerous parts similar to community settings, storage, and safety.
With Linux digital machines, you may configure community settings to fit your wants. The three important choices for community settings are bridged, NAT (Community Deal with Translation), and host-only.
###
Configuring Community Settings
Configuring community settings permits you to management how your digital machine interacts with the bodily community. You’ll be able to select from three important choices: bridged, NAT, and host-only.
-
Bridged networking connects your digital machine on to the bodily community. This enables your digital machine to speak with different gadgets on the community, identical to a bodily machine.
-
NAT (Community Deal with Translation) networking assigns a personal IP deal with to your digital machine, permitting it to speak with the bodily community whereas conserving your personal community hidden from the surface.
-
Host-only networking connects your digital machine to the bodily machine’s community stack, however no different gadgets on the bodily community can talk along with your digital machine.
When selecting a community setting, contemplate the necessities of your digital machine and the safety stage you need to preserve.
###
Establishing SSH and Different Community Companies
To arrange SSH and different community companies, you have to to configure the community settings of your digital machine. Observe these steps:
1. Guarantee your digital machine is configured to make use of a bridged, NAT, or host-only community setting.
2. Arrange a static IP deal with to your digital machine.
3. Configure the SSH server to pay attention on a selected port.
4. Take a look at the SSH connection out of your host machine to your digital machine.
###
Configuring Storage Settings
Configuring storage settings is essential for organising your digital machine’s file system. You’ll be able to configure storage settings to fit your wants, together with digital arduous disk and CD/DVD drives.
####
Digital Exhausting Disk
A digital arduous disk is a file that simulates a bodily arduous drive. You’ll be able to create a digital arduous disk utilizing numerous codecs similar to VMDK, VDI, or VHD.
– Mounted-size arduous disk: Allocates a set quantity of house on the host machine’s disk.
– Dynamic arduous disk: Allocates house as wanted, however might result in fragmentation.
– Skinny-provisioned arduous disk: Allocates house solely when information is written, decreasing the chance of fragmentation.
####
CD/DVD Drives
A CD/DVD drive in a digital machine is a digital system that permits you to mount and entry CDs or DVDs.
– Host drive: Permits entry to the host machine’s CD/DVD drive.
– ISO file: Permits mounting of ISO information.
###
Creating Snapshots and Cloning Digital Machines
Snapshots and cloning can help you create copies of your digital machine at a sure time limit.
###
Creating Snapshots
A snapshot is a duplicate of the present state of the digital machine. You’ll be able to create a snapshot at any time limit and revert again to that time later.
###
Cloning Digital Machines
Cloning creates a brand new digital machine that’s a precise copy of the unique.
Cloning may be helpful if that you must create a brand new machine with the identical settings and configuration. Nevertheless, observe that it might nonetheless have a distinct UUID (Universally Distinctive Identifier).
Managing Linux Digital Machines
Managing Linux digital machines requires a deep understanding of the working system’s intricacies and the virtualization software program getting used. Efficient administration allows system directors to optimize efficiency, troubleshoot points, and make sure the safety and integrity of the digital surroundings.
Viewing Useful resource Utilization and Efficiency Metrics
To handle and monitor Linux digital machines, it’s essential to have real-time visibility into system useful resource utilization, together with CPU, reminiscence, and disk utilization. This may be achieved through the use of numerous command-line instruments and graphical interfaces:
- The
primecommand gives a real-time view of system processes, CPU utilization, and reminiscence consumption. - The
freecommand gives info on reminiscence and disk utilization. - The
htopcommand, an interactive model ofprime, permits for extra in-depth evaluation and filtering of system processes. - The
xrdpandrdpinstructions facilitate distant entry to graphical consoles and allow system directors to watch digital machine efficiency from wherever.
Taking and Restoring Snapshots
Snapshots are a significant function in virtualization, permitting system directors to seize the state of a digital machine at a specific time limit. This function is especially helpful for backup and catastrophe restoration functions. The method of taking and restoring snapshots entails:
- Utilizing the virtualization software program’s built-in snapshot device, similar to VMware vCenter Converter or VirtualBox.
- Making a snapshot by freezing the digital machine’s state, which incorporates the RAM, disk, and different system settings.
- Restoring a snapshot by reverting the digital machine to its earlier state.
Cloning and Creating Templates
Cloning and creating templates are important for effectively managing Linux digital machines. Cloning entails creating a replica of an present digital machine, whereas creating templates entails making a snapshot of a digital machine that can be utilized to create new digital machines. The advantages of cloning and creating templates embrace:
- Streamlining the digital machine creation course of by reusing present configurations.
- Guaranteeing consistency throughout a number of digital machines by standardizing configurations.
- Enhancing effectivity by decreasing the quantity of guide configuration required.
A well-managed Linux digital machine surroundings can considerably enhance efficiency, cut back downtime, and improve general system safety.
Linux Digital Machine Safety
Securing Linux digital machines is essential to guard delicate information and stop potential safety threats. A compromised digital machine can have extreme penalties, together with information breaches, unauthorized entry, and disruptions to essential companies. To mitigate these dangers, it’s important to implement strong safety measures and observe finest practices for managing and monitoring Linux digital machines.
Setting Robust Passwords
A powerful password is the primary line of protection towards unauthorized entry to a Linux digital machine. To make sure the safety of your digital machine, you need to set sturdy passwords for all customers, together with the foundation account. A powerful password ought to meet the next standards:
- Be at the least 8 characters lengthy
- Comprise a mixture of uppercase and lowercase letters
- Embrace numbers and particular characters
- Be distinctive and never simply guessable
It’s endorsed to make use of a password supervisor to generate and retailer complicated passwords. Keep away from utilizing widespread passwords or simply guessable info, similar to your identify or birthdate.
Proscribing Entry to Delicate Information
Linux digital machines usually retailer delicate information, similar to database credentials, encryption keys, and confidential paperwork. To forestall unauthorized entry to those information, you need to implement restrictive file permissions and entry controls. Use the next methods to restrict entry to delicate information:
- Use the umask command to set default file permissions
- Use the chown command to vary file possession and permissions
- Use the chmod command to switch file permissions
- Use entry management lists (ACLs) to grant or deny entry to particular customers or teams
By implementing restrictive file permissions and entry controls, you may stop unauthorized entry to delicate information and defend your digital machine from potential safety threats.
Implementing Firewall Guidelines
Firewall guidelines play an important position in securing Linux digital machines by controlling incoming and outgoing community visitors. A well-configured firewall can stop unauthorized entry to your digital machine, block malicious visitors, and restrict the publicity of delicate information.
blockquote>”The very first thing you do whenever you’re coping with a hostile surroundings is to arrange a firewall.” – Linus Torvalds
To implement firewall guidelines, you need to use the iptables command or a firewall administration device like ufw. Create guidelines to:
- Block incoming visitors on pointless ports and companies
- Permit outgoing visitors to important companies and locations
- Implement stateful packet inspection to detect and block malicious visitors
By implementing firewall guidelines, you may improve the safety of your Linux digital machine and stop potential safety threats.
Monitoring and Analyzing System Logs
System logs present invaluable details about safety incidents, errors, and different occasions occurring in your Linux digital machine. To detect potential safety threats and stop information breaches, you need to commonly monitor and analyze system logs. Use the next instruments to gather and analyze system logs:
- syslog-ng
- logrotate
- grep
- awk
By monitoring and analyzing system logs, you may:
- Determine potential safety threats and vulnerabilities
- Detect and reply to safety incidents
- Optimize system efficiency and cut back errors
Commonly monitoring and analyzing system logs is crucial to sustaining a safe and dependable Linux digital machine.
Linux Digital Machine Backup and Restoration
Linux digital machines are essential parts of recent IT infrastructure, and their availability, reliability, and safety can’t be compromised. Due to this fact, it’s important to implement strong backup and restoration methods to make sure that these digital machines are all the time up and operating.
Significance of Block-Stage Backups
Block-level backups are a kind of backup that focuses on backing up the uncooked information blocks of a digital machine’s disk, relatively than particular person information. This strategy is extremely environment friendly and efficient for backing up massive information units, because it eliminates the necessity to scan and backup particular person information. Block-level backups are notably helpful for digital machines that retailer massive quantities of information, similar to databases, file servers, and video enhancing workstations.
Determine the digital machine’s disk storage:This may be completed by accessing the digital machine’s settings or configuration file. The disk storage is often situated in a format similar to VMDK or VDI.Use a backup device:Choose a dependable backup device that helps block-level backups, similar to Veeam or Acronis. This device will scan the digital machine’s disk and establish the info blocks that must be backed up.Configure the backup job:Specify the digital machine, the disk storage, and the backup frequency. The backup device will then execute the backup job and create a constant backup of the digital machine’s information.
Advantages of Incremental Backups
Incremental backups are a kind of backup that backs up solely the modifications made to a digital machine’s information because the final full backup. This strategy is extremely environment friendly and efficient for backing up massive information units, because it reduces the quantity of information that must be backed up. Incremental backups are notably helpful for digital machines that have frequent modifications, similar to improvement environments, testing labs, and manufacturing servers.
Decide the backup frequency:Specify how usually the incremental backup ought to run, similar to day by day or weekly.Determine the bottom picture:Choose the bottom picture from which to carry out the incremental backup. This picture needs to be a constant and full backup of the digital machine’s information.Run the incremental backup:Execute the backup job and let the device create an incremental backup of the modifications made to the digital machine’s information because the final full backup.
Restoring from Snapshots
Snapshots are point-in-time copies of a digital machine’s state, together with its reminiscence, disk, and community configuration. Restoring from snapshots is a extremely environment friendly and efficient method to get better a digital machine from a earlier state. This strategy is especially helpful for digital machines that have frequent information corruption or {hardware} failures.
Determine the snapshot:Choose the snapshot from which to revive. This snapshot needs to be a constant and full copy of the digital machine’s state.Run the restore job:Execute the restore job and let the device recreate the digital machine’s state from the snapshot.Confirm the restore:As soon as the restore job completes, confirm that the digital machine is correctly restored and functioning as anticipated.
Cloning Digital Machines
Cloning digital machines is a extremely environment friendly and efficient method to create a replica digital machine with the identical configuration, reminiscence, and disk settings. This strategy is especially helpful for digital machines that require similar setup, similar to improvement environments, testing labs, and manufacturing servers.
Determine the supply digital machine:Choose the digital machine to be cloned. This digital machine ought to have the specified configuration, reminiscence, and disk settings.Run the clone job:Execute the clone job and let the device create a replica digital machine with the identical configuration, reminiscence, and disk settings.Confirm the clone:As soon as the clone job completes, confirm that the cloned digital machine is correctly created and functioning as anticipated.
Actual World Purposes of Linux Digital Machines
Linux digital machines have grow to be an important device in numerous industries attributable to their flexibility, scalability, and cost-effectiveness. On this part, we are going to discover a number of real-world functions of Linux digital machines and talk about their advantages and challenges in several situations.
Case Research in Training
Linux digital machines have been extensively adopted in academic establishments attributable to their ease of use and suppleness. They permit educators to create a simulated studying surroundings that mimics real-world situations, permitting college students to realize sensible expertise and develop important expertise.
- Simulated lab environments: Linux digital machines allow educators to create simulated lab environments that permit college students to apply and be taught with out the necessity for bodily tools. This strategy reduces the monetary burden on academic establishments and gives college students with a secure and managed surroundings to experiment and be taught.
- Virtualized scholar workstations: Linux digital machines can be utilized to create virtualized scholar workstations that present college students with entry to a shared computing surroundings. This strategy allows college students to work on initiatives and assignments in a collaborative and safe method.
- Lab automation: Linux digital machines can be utilized to automate lab procedures, releasing up educators to deal with educating and mentoring college students.
Case Research in Analysis and Growth
Linux digital machines have grow to be a necessary device in analysis and improvement (R&D) attributable to their excessive efficiency and suppleness. They permit researchers to create complicated, scalable environments that may be simply duplicated and shared with colleagues.
- Excessive-performance simulations: Linux digital machines can be utilized to create high-performance simulations that allow researchers to mannequin complicated programs and phenomena. This strategy has been utilized in numerous fields, together with local weather modeling, fluid dynamics, and supplies science.
- Giant-scale information evaluation: Linux digital machines can be utilized to carry out large-scale information evaluation, enabling researchers to course of and analyze huge quantities of information rapidly and effectively.
- Collaborative environments: Linux digital machines can be utilized to create collaborative environments that allow researchers to work collectively on initiatives and share assets.
Case Research in Growth and Deployment
Linux digital machines have grow to be a necessary device in improvement and deployment attributable to their flexibility and scalability. They permit builders to create and take a look at complicated programs and functions rapidly and effectively.
- DevOps environments: Linux digital machines can be utilized to create DevOps environments that allow builders to check and deploy functions rapidly and effectively.
- Steady Integration and Steady Deployment (CI/CD): Linux digital machines can be utilized to implement CI/CD pipelines that allow builders to automate the testing and deployment of functions.
- Cloud-native functions: Linux digital machines can be utilized to create cloud-native functions which can be scalable, safe, and extremely out there.
Advantages and Challenges
Linux digital machines provide a number of advantages, together with flexibility, scalability, and cost-effectiveness. Nevertheless, in addition they current a number of challenges, together with compatibility points, safety issues, and excessive upkeep necessities.
- Advantages:
- Flexibility: Linux digital machines may be simply cloned and customised to fulfill particular wants.
- Scalability: Linux digital machines may be scaled up or down to fulfill altering necessities.
- Price-effectiveness: Linux digital machines may be created and managed at a decrease price than bodily {hardware}.
- Challenges:
- Compatibility points: Linux digital machines is probably not appropriate with all {hardware} and software program.
- Safety issues: Linux digital machines could also be weak to safety threats, together with malware and unauthorized entry.
- Upkeep necessities: Linux digital machines require common upkeep, together with updates and patching.
Future Growth and Tendencies
The adoption of Linux digital machines is anticipated to proceed rising in numerous industries, pushed by their flexibility, scalability, and cost-effectiveness. Future developments and developments embrace the usage of Linux digital machines in Edge computing, AI, and IoT functions.
Edge Computing
Linux digital machines can be utilized to create Edge computing environments that allow information processing and evaluation on the fringe of the community, decreasing latency and bettering efficiency.
AI and Machine Studying
Linux digital machines can be utilized to create AI and machine studying environments that allow builders to coach and deploy AI fashions rapidly and effectively.
IoT and Embedded Programs
Linux digital machines can be utilized to create IoT and embedded programs environments that allow builders to create and handle complicated programs and functions rapidly and effectively.
Finest Practices for Utilizing Linux Digital Machines
When working with Linux digital machines, having a stable understanding of one of the best practices is crucial for making certain easy operation, environment friendly useful resource utilization, and strong safety. By following these pointers, you may keep away from widespread pitfalls and take advantage of out of your virtualization efforts.
Selecting the Appropriate Software program
When choosing a virtualization software program, contemplate your particular wants and the kind of Linux distribution you are planning to make use of. Some well-liked choices embrace
- VirtualBox, which gives a variety of options and is obtainable for a number of platforms.
- KVM, an open-source answer that is notably appropriate for Linux programs.
- VMware, a strong choice with sturdy safety features and excessive efficiency capabilities.
Every of those choices has its strengths and weaknesses, and choosing the proper one to your wants can significantly influence your general expertise.
Configuring {Hardware}
When configuring your digital {hardware}, it is important to strike a steadiness between efficiency and useful resource utilization. Contemplate the next factors:
- Assigning enough RAM to your VM: Be sure that you allocate sufficient reminiscence to match the necessities of your Linux distribution and functions. Inadequate RAM can result in gradual efficiency and even crashes.
- Selecting the right CPU settings: Choosing the fitting CPU mode (e.g., VT-x or AMD-V) and allocating enough CPU assets can considerably influence efficiency.
- Establishing storage: Resolve on the storage sort and allocation to your VM, contemplating elements similar to pace, capability, and sturdiness.
Correct configuration of your digital {hardware} can significantly influence your digital machine’s efficiency and general usability.
Managing Digital Machines
Efficient administration of your digital machines is essential for sustaining a easy operation and making certain safety. Contemplate the next methods:
- Monitoring useful resource utilization: Commonly examine your VM’s useful resource utilization to establish potential bottlenecks or areas for optimization.
- Implementing backup and restoration procedures: Develop a sturdy backup and restoration plan to guard your VM’s information and guarantee enterprise continuity.
- Imposing safety finest practices: Commonly replace your VM’s software program, configure firewalls, and use sturdy passwords to stop unauthorized entry.
Correct administration of your digital machines may help stop points, guarantee safety, and optimize useful resource utilization.
Troubleshooting Frequent Points
When points come up along with your digital machines, it is important to strategy troubleshooting in a methodical and environment friendly method. Contemplate the next methods:
- Reviewing system logs: Analyzing system logs can present invaluable insights into potential causes of points.
- Checking for updates: Guaranteeing your VM’s software program is up-to-date can resolve many widespread points.
- Disabling pointless companies: Figuring out and disabling pointless companies may help stop conflicts and enhance efficiency.
By using these finest practices and methods, you may reduce the chance of widespread points and guarantee a easy operation to your Linux digital machines.
Final Conclusion
In conclusion, Linux for digital machine guarantees a wealth of prospects for customers and directors alike. By understanding the intricacies of digital machine configurations, administration, and safety, we will unlock the complete potential of those digital entities. As we proceed to evolve and enhance the artwork of virtualization, we are going to undoubtedly see much more outstanding functions of Linux for digital machine.
Normal Inquiries
What’s the finest virtualization software program for Linux?
The perfect virtualization software program for Linux is determined by particular person wants and preferences. Widespread choices embrace VirtualBox, VMware, and KVM. Every software program has its strengths and weaknesses, and customers ought to analysis and select the one which fits their necessities.
How do I configure community settings in a Linux digital machine?
To configure community settings in a Linux digital machine, you may observe these steps: First, create a brand new digital community interface within the visitor working system. Then, configure the IP deal with and subnet masks in accordance with your community settings. Lastly, confirm the community connection by pinging a close-by host or a public IP deal with.
Can I run a number of working programs on a single digital machine?
Sure, you may run a number of working programs on a single digital machine, however this may increasingly require some tweaking of the digital machine settings. It’s best to select an working system that helps multi-booting and create separate digital disk pictures for every working system. Moreover, you might want to regulate the CPU and reminiscence settings to make sure that every working system has enough assets.
How do I safe my Linux digital machine?
To safe your Linux digital machine, you need to implement the next finest practices: Use sturdy passwords for all customers, together with the foundation person. Allow authentication and authorization utilizing instruments like PAM and SELinux. Commonly replace your digital machine’s packages and plugins. Lastly, monitor system logs and alerts for potential safety threats.