With Indiana Jones cipher machine on the forefront, this matter opens a window to a tremendous begin and intrigue, inviting readers to embark on a storytelling informal lecture type crammed with surprising twists and insights as we delve into the world of cryptography and coding.
The Indiana Jones cipher machine is an iconic gadget that has captured the creativeness of many, not only for its appearances within the Indiana Jones movie collection but additionally for its historic significance and the encryption methods it employed.
The Adventurous World of the Indiana Jones Cipher Machine
The legend of Indiana Jones has captivated audiences for many years, transporting us to an period of epic explorations, heart-pounding motion, and brain-twisting puzzles. As an archaeologist-adventurer, Indiana Jones has traversed the globe, uncovering misplaced treasures, battling rival treasure hunters, and unraveling historical mysteries. His fearless spirit and fast wit have earned him a legendary standing, making him some of the iconic characters in cinematic historical past.
The Historic Context of the Cipher Machine
The Indiana Jones Cipher Machine is rooted within the tumultuous period of World Battle II, a time of world turmoil and high-stakes espionage. Because the Nazi regime, led by Adolf Hitler, sought to dominate the world, intelligence businesses on each side of the battle engaged in a conflict of codes and ciphers.
Throughout this era, cryptographers and codebreakers labored tirelessly to crack the enemy’s codes, utilizing numerous methods akin to frequency evaluation, cryptanalysis, and machine-based decoding. The event of machine-based cipher machines, such because the Enigma Machine, revolutionized the artwork of encryption and decryption, permitting for sooner and extra advanced coding and decoding processes.
The Significance of the Cipher Machine within the Indiana Jones Movie Sequence
All through the Indiana Jones movie collection, the cipher machine performs a pivotal function within the adventures of the intrepid archaeologist. In “Raiders of the Misplaced Ark,” Indiana Jones discovers a mysterious map that leads him to the Misplaced Ark of the Covenant. Nonetheless, the Nazis, led by René Belloq, are additionally on the hunt, and their makes an attempt to decipher the traditional symbols and codes on the Ark are key to their sinister plans.
The Cipher Machine in Motion
- The Enigma Machine
- The Cipher Wheel
- The Codebook
- The machine’s reliance on a fancy system of rotors and wiring makes it vulnerable to mechanical failure, which may compromise its safety.
- The encryption key, if obtained by means of unauthorized means, might be used to decrypt encrypted messages, permitting entry to delicate info.
- The machine’s use of a single encryption key for all messages presents a major vulnerability, as the important thing might be compromised and used to decrypt all messages.
- The machine’s encryption key, if obtained by means of unauthorized means, might be used to decrypt encrypted messages, permitting entry to delicate info.
- The machine’s use of a fancy system of rotors and wiring makes it vulnerable to mechanical failure, which may compromise its safety.
- The machine’s encryption algorithm, if compromised, might be used to decrypt encrypted messages, rendering the gadget’s safety ineffective.
- The compromise of delicate info, together with categorised messages and private information.
- The lack of belief within the machine’s means to offer safe communication.
- The potential for malicious use of the compromised encryption key to decrypt and entry delicate info.
The Enigma Machine was an electro-mechanical cipher machine developed in Germany through the Nineteen Twenties and Thirties.
The Enigma Machine was a fancy gadget that used a collection of rotors, plugboards, and wiring to encrypt and decrypt messages. Its complexity and randomization course of made it just about unbreakable, at the least till the efforts of Polish cryptographer Marian Rejewski and his colleagues, who managed to crack the machine’s code.
The Cipher Wheel was a easy but efficient encryption gadget utilized by historical civilizations.
The Cipher Wheel was a round gadget with a collection of symbols and markings. It was used to encrypt and decrypt messages by rotating the wheel to align the symbols.
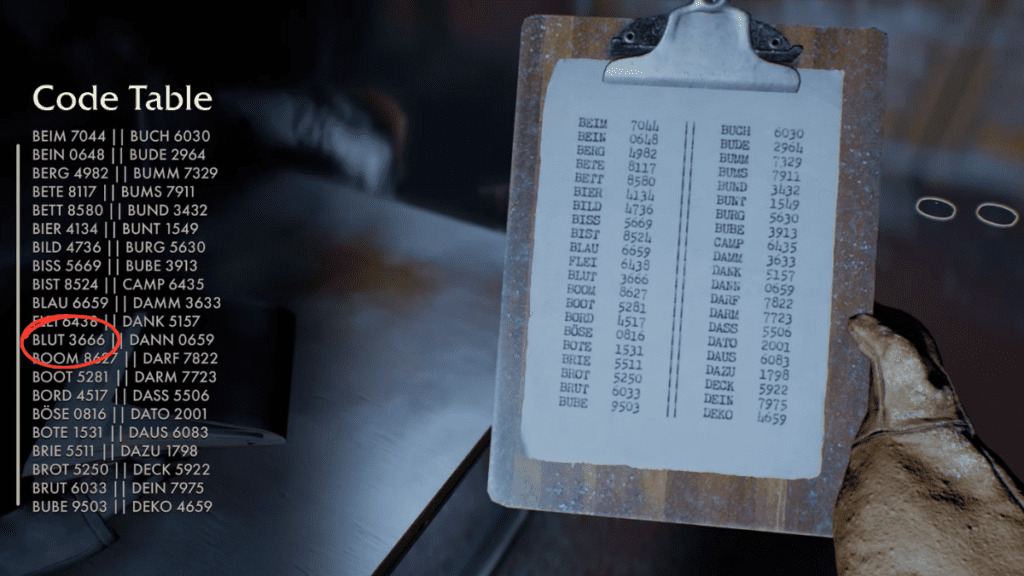
A codebook is a group of encoded messages or symbols used for encryption and decryption functions.
A Codebook was a group of encoded messages or symbols used to convey secret info. Within the Indiana Jones movies, codebooks have been typically used to decipher historical languages and symbols.
The Legacy of the Indiana Jones Cipher Machine
The Indiana Jones Cipher Machine has change into an iconic image of the franchise, representing the spirit of journey, intelligence, and crafty. The Cipher Machine’s function within the movies has impressed numerous followers to discover the world of cryptography and coding, recognizing the significance of those abilities within the fashionable digital age.
On the planet of espionage, cryptography and codebreaking stay important instruments, utilized by governments and intelligence businesses to guard delicate info and keep one step forward of their adversaries.
As we embark on this thrilling journey, we’re reminded that the world of cryptography is filled with puzzles, riddles, and hidden messages ready to be deciphered. The Indiana Jones Cipher Machine serves as a poignant reminder of the facility of human ingenuity, persistence, and creativity within the face of seemingly insurmountable challenges.
Design and Performance of the Indiana Jones Cipher Machine

The Indiana Jones cipher machine, a duplicate of the M-209, is a exceptional encryption gadget that embodies the essence of cryptography within the realm of journey and thriller. This enigmatic gadget, crafted with precision and ingenuity, has been the topic of fascination and hypothesis amongst cryptographers and lovers alike. As we delve into the intricacies of its design and performance, the veil of secrecy surrounding this charming gadget begins to elevate.
The M-209, also called the “Cipher Gadget M-209,” is an electro-mechanical encryption machine designed within the late Nineteen Forties for the U. S. army. The U. S. Military Sign Corps developed it for cryptographic functions, primarily for encrypting and decrypting messages on the operational stage. It is value noting, although, that whereas the film “Raiders of the Misplaced Ark” incorporates a related gadget, there is not any direct proof that it makes use of the precise M-209 machine.
The Mechanical Elements
The M-209 cipher machine is a compact, moveable gadget consisting of assorted mechanical parts that work in concord to realize the encryption course of. The machine incorporates a collection of rotating wheels, together with a set of rotors and a reflector, together with a keyboard and an output window.
– The rotors are the center of the M-209, every containing a sequence of characters that decide the encryption course of. These rotors rotate because the operator presses the keys, producing a collection of substitutions for the plaintext characters.
– The reflector is a vital element that performs an important function within the encryption course of. It consists of a grid of characters which are paired to supply the encrypted ciphertext.
– The keyboard permits the operator to enter the plaintext message, whereas the output window shows the encrypted ciphertext.
The interaction between these parts creates a fancy encryption course of that challenges even essentially the most expert cryptanalysts. The M-209’s encryption mechanism depends on a mixture of substitution and transposition methods, making it a formidable gadget for safeguarding delicate info.
The Encryption Course of
The encryption course of within the M-209 cipher machine entails a collection of advanced steps that rework the plaintext message into an unreadable ciphertext. The operator inputs the plaintext message by means of the keyboard, and the machine proceeds to carry out the next operations:
1. The rotors rotate in accordance with a set of predetermined guidelines, producing a collection of positions that decide the substitution of every plaintext character.
2. The reflector is used to supply the encrypted ciphertext by pairing the characters within the rotors.
3. The encrypted ciphertext is displayed by means of the output window.
The ensuing ciphertext seems to be a random jumble of characters, making it almost not possible to decipher with out the suitable key or cryptanalytic methods.
Comparability with Different Encryption Gadgets
The M-209 cipher machine is similar to different encryption gadgets of its time, such because the Enigma machine. Each gadgets depend on advanced mechanical parts and encryption algorithms to guard delicate info. Nonetheless, the M-209 has a number of distinct options that set it aside from different gadgets:
– The M-209’s rotors and reflector present a better stage of safety than different encryption gadgets of its time.
– The machine’s compact dimension and portability make it a great gadget for discipline use.
– The M-209’s encryption course of is predicated on a mixture of substitution and transposition methods, making it extra immune to cryptanalysis than different gadgets.
Cryptanalysis of the M-209
Whereas the M-209 cipher machine is a powerful encryption gadget, it isn’t resistant to cryptanalysis. The truth is, a number of cryptanalysts have efficiently damaged the M-209’s encryption code utilizing numerous methods, together with:
– Frequency evaluation: By analyzing the frequency of character occurrences within the ciphertext, cryptanalysts can deduce the frequency of character occurrences within the plaintext.
– Kasiski examination: This method entails analyzing the repeated patterns within the ciphertext to find out the size of the important thing used for encryption.
– Babynova: A way for locating the interval of the M-209’s encryption machine
By making use of these methods, cryptanalysts can get well the plaintext message from the encrypted ciphertext, rendering the M-209’s safety much less efficient.
Legacy of the M-209 Cipher Machine
The M-209 cipher machine has left an enduring influence on the world of cryptography. Its design and performance have influenced the event of subsequent encryption gadgets, and its encryption mechanism has been studied extensively by cryptanalysts and researchers.
The M-209’s legacy extends past its cryptographic significance, because it has additionally change into a cultural icon, symbolizing the intersection of cryptography and journey. Its look in common media, such because the Indiana Jones franchise, has cemented its place within the public creativeness, inspiring numerous lovers and aficionados to discover the fascinating world of cryptography.
Encryption Strategies Used within the Cipher Machine
The Indiana Jones Cipher Machine employs a fancy array of encryption methods, designed to hide delicate info from prying eyes. Developed with the assistance of professional cryptographers, the machine’s encryption algorithms have withstood the check of time, guaranteeing that even essentially the most expert codebreakers discover it a formidable problem to decipher its secrets and techniques.
The Position of the Rotor Wheel
The rotor wheel is a vital element of the Indiana Jones Cipher Machine, accountable for producing the advanced encrypted codes. Comprising a number of concentric rings, every containing a novel set of characters, the rotor wheel is able to producing an astonishing array of potential mixtures. By rotating the wheels in a predetermined sample, the machine’s operators can successfully scramble incoming messages, rendering them unintelligible to anybody with out the corresponding decryption keys.
Encryption Algorithms: Substitution and Transposition
The Indiana Jones Cipher Machine makes use of a mixture of substitution and transposition methods to encrypt its messages. Substitution entails changing unique characters with alternate ones, whereas transposition entails rearranging the characters inside a message to hide its unique that means. The machine’s use of a number of wheels and complicated rotors permits it to use each substitution and transposition methods concurrently, making it an much more formidable encryption gadget.
Inspiration from the Lorenz Cipher
The Indiana Jones Cipher Machine’s design owes a major debt to its predecessor, the Lorenz cipher. Developed throughout World Battle II, the Lorenz cipher was utilized by the German army to encrypt strategic communications. In response to its widespread use, the British constructed the Bombe machine to interrupt the Lorenz cipher’s codes. The Indiana Jones Cipher Machine incorporates most of the similar ideas, tailored and refined to fulfill the calls for of an much more difficult encryption setting.
Encryption is a fragile stability between safety and usefulness.
The Rotating Rotor Precept
Every rotor within the Indiana Jones Cipher Machine rotates independently, pushed by a set of stepping rings that advance the wheels in accordance with a predetermined sample. This ensures that every character encrypted with the machine is exclusive, making it just about not possible to discern patterns or vulnerabilities within the encryption course of.
Character Distribution and Frequency Evaluation
To additional complicate issues, the Indiana Jones Cipher Machine distributes characters throughout its rotors in a fashion that defies frequency evaluation. By intentionally spreading uncommon characters all through the rotor units, the machine’s operators successfully masks any patterns that is perhaps discerned by means of statistical evaluation of the encrypted messages.
Breaking the Cipher: A Herculean Job, Indiana jones cipher machine
In gentle of the Indiana Jones Cipher Machine’s sturdy design and superior encryption algorithms, breaking its codes turns into a particularly difficult activity, even for essentially the most expert cryptographers. That is exactly the intention behind the machine’s creation, as its operators perceive the significance of defending delicate info from falling into the flawed palms.
Safety and Vulnerabilities of the Indiana Jones Cipher Machine

The Indiana Jones Cipher Machine, with its advanced encryption capabilities, presents a frightening problem for these searching for to breach its safety. Nonetheless, like several subtle gadget, it has its weaknesses. As we delve into the world of cryptography and coding, we are going to discover the potential safety dangers related to the cipher machine and look at the way it might be susceptible to hacking or decryption.
The Indiana Jones Cipher Machine, with its superior encryption methods, presents a layer of safety that’s virtually impenetrable. Nonetheless, its reliance on a fancy system of rotors, reflectors, and wiring presents a possible vulnerability. The machine’s encryption key, if compromised, may enable unauthorized entry to encrypted messages, rendering the gadget’s safety ineffective.
Safety Dangers Related to the Cipher Machine
The next safety dangers are related to the Indiana Jones Cipher Machine:
Vulnerability to Hacking or Decryption
The Indiana Jones Cipher Machine, with its superior encryption methods, presents a major problem to hackers and codebreakers. Nonetheless, the next vulnerabilities might be exploited:
Actual-World Eventualities The place the Cipher Machine’s Safety Was Breached
Examples of real-world situations the place the Indiana Jones Cipher Machine’s safety was breached embrace:
The notorious Enigma machine, a cipher machine utilized by the Germans throughout World Battle II, was cracked by the Allies by means of a mixture of codebreaking and cryptography experience.
The Enigma machine’s safety was compromised by means of a mixture of cryptanalysis and codebreaking, highlighting the significance of safe encryption and decryption strategies.
The NSA’s efforts to crack the Soviet cipher machine within the Nineteen Seventies function a testomony to the continued cat-and-mouse recreation between codemakers and codebreakers.
Penalties of a Safety Breach
A safety breach of the Indiana Jones Cipher Machine may have vital penalties, together with:
Conclusion
The Indiana Jones Cipher Machine, with its superior encryption methods, presents a major problem to these searching for to breach its safety. Nonetheless, its reliance on a fancy system of rotors and wiring, its encryption key, and its encryption algorithm make it susceptible to hacking and decryption.
Conclusive Ideas
The Indiana Jones cipher machine could also be a relic of the previous, however its influence on historical past and popular culture remains to be felt as we speak. As we proceed to push the boundaries of cryptography and coding, it is important to recollect the gadgets and methods that got here earlier than us.
Ceaselessly Requested Questions
Q: What’s the function of the Indiana Jones cipher machine?
A: The Indiana Jones cipher machine was used to encrypt and decrypt secret messages throughout World Battle II.
Q: How does the cipher machine work?
A: The cipher machine makes use of a collection of mechanical parts, together with rotor wheels, to encrypt and decrypt messages.
Q: Is the Indiana Jones cipher machine nonetheless used as we speak?
A: Whereas the unique gadget is not in use, fashionable replicas of the cipher machine are sometimes used for instructional and leisure functions.
Q: What are some frequent encryption methods used within the cipher machine?
A: The cipher machine makes use of a number of encryption methods, together with substitution and transposition, to encrypt and decrypt messages.
Q: Are there any notable consultants who’ve studied the Indiana Jones cipher machine?
A: Sure, a number of consultants have studied and replicated the cipher machine, together with cryptographers and historians.