How the Enigma Machine Was Cracked is an intriguing story that unravels in a fascinating method, drawing readers right into a story that mixes complexity, strategic considering, and willpower. The Enigma machine, a German army innovation, was used to safe communication throughout World Warfare II, making it a urgent subject for the Allied forces.
The Enigma machine’s keyboard format and performance are an important side of its operation, with the machine producing a fancy encryption that has been the topic of intensive evaluation and examine. Regardless of its significance, deciphering the Enigma code was a frightening job, presenting quite a few challenges for cryptographic analysts and highlighting the significance of persistence and modern problem-solving.
Introduction
The Enigma machine performed a pivotal position in World Warfare II, serving as a important device for safe communication between German army models and command facilities. Developed within the Nineteen Twenties by German engineer Arthur Scherbius, the Enigma machine used a fancy system of rotors, wiring, and substitution tables to encode messages, making them nearly unbreakable.
The Enigma Machine
The German army adopted the Enigma machine attributable to its perceived unbreakability, utilizing it for high-level communication. This was particularly essential for the German army, which was keen to take care of secrecy in its operations and plans through the warfare. The machine’s major operate was to substitute alphabetic characters with different alphabetic characters, making it troublesome for unauthorized events to decipher the messages.
Encryption and Decryption Course of
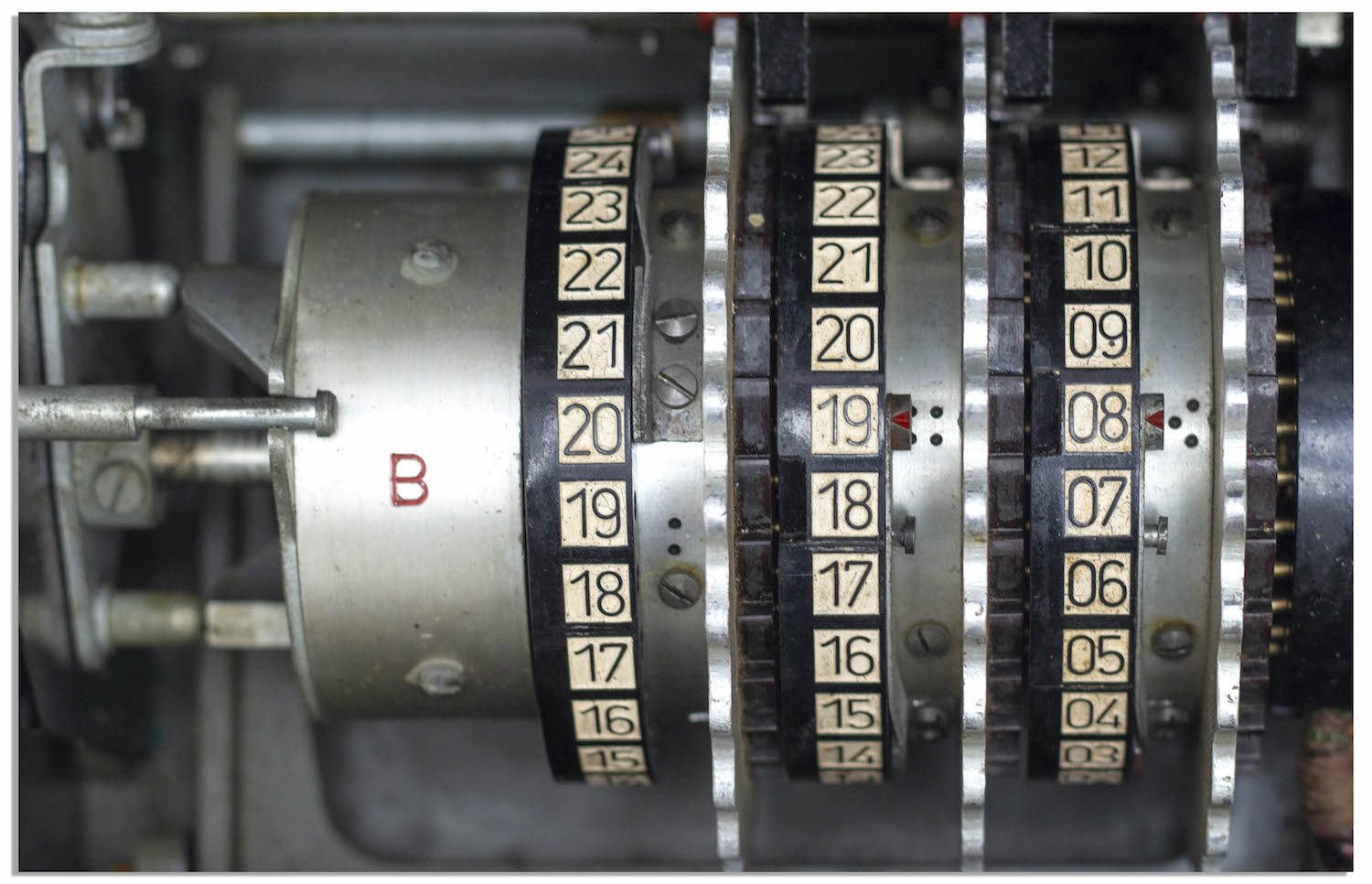
The Enigma machine employed a polyalphabetic substitution cipher, which concerned the usage of a number of rotors, a wiring system, and a keyboard to encrypt messages. The rotors have been accountable for shifting the character positions, creating a novel substitution sample for every character entered. Every rotor had a selected variety of wiring connections, which added to the complexity of the encryption course of. The outcome was an encoded message that appeared random to outsiders, requiring in depth data of the machine’s inside workings and settings to precisely decrypt.
Operational Particulars
On daily basis, the German army would arrange the machine, deciding on particular rotors, wiring, and ring settings. The machine’s keyboard allowed for environment friendly enter of characters, and the substitution tables ensured that every character was changed with a brand new one, following a predetermined sequence. The encoded message would then be fed by way of a machine like an Enigma machine through radio transmission. This ensured that data was saved secret, even when intercepted by enemy forces.
Impression and Limitations
Regardless of being unbreakable to most people, the Enigma machine was not foolproof. The machine’s inside workings and settings may very well be deduced by way of rigorous work and collaboration, ultimately enabling the Allies to crack the code. German operators weren’t conscious of this risk, usually utilizing the Enigma machine for routine communications. Whereas the Enigma machine served German army targets, limitations existed, together with the potential for human error, upkeep points, and the event of rival encryption strategies.
Limitations of Human-Operated Machines
The Enigma machine relied closely on human operators, who would manually set the rotors, wiring, and ring settings every day. Human error and variations in settings may result in difficulties in deciphering messages. As German forces expanded their geographical attain, coordinating operations throughout distant areas grew to become more and more difficult. This led to cases of confusion and miscommunication attributable to machine settings being set incorrectly. Moreover, because the Allies gathered essential details about the machine’s operation, the German army’s reliance on the Enigma machine grew more and more weak.
Key Gamers and Their Contributions
A number of key people performed an important position in deciphering Enigma messages. Polish mathematicians Marian Rejewski, Jerzy Różycki, and Henryk Zygalski have been among the many first to crack the Enigma code by way of painstaking work and collaboration. Their efforts ultimately reached the British intelligence company, the place codebreakers like Alan Turing used the supplied data to develop a working model of the Bombe machine, a mechanical machine particularly designed to automate the method of deciphering the Enigma code.
British Intelligence Company and Codebreaking Efforts
The British codebreaking company (additionally known as the Authorities Code and Cypher College, or GC & CS), situated at Bletchley Park, spearheaded the hassle to crack the Enigma code. With help from Polish cryptographers and mathematicians, they made use of cryptanalysis strategies and machine growth. The British group’s work centered on utilizing the Bombe machine, alongside human operators, to quickly course of and crack intercepted Enigma communications. Their efforts considerably altered the tide of World Warfare II, in the end offering worthwhile data to the Allied forces.
Construction and Operation
The Enigma machine was a fancy cryptographic machine that performed an important position in securing German communications throughout World Warfare II. Its distinctive construction and operation made it one of the vital safe encryption programs of its time. The machine consisted of a keyboard, a plugboard, and a rotor system that mixed to scrambles the textual content entered into the machine.
At its core, the Enigma machine was an electro-mechanical cipher machine that used a sequence of rotors, wiring, and substitution tables to encrypt messages. The machine’s keyboard format featured 26 keys, one for every letter of the alphabet, in addition to a couple of further keys for widespread punctuation marks and symbols. The plugboard, situated on the entrance of the machine, was a small panel with a sequence of sockets that allowed the operator to attach the letters in a selected order. This created a novel substitution desk that modified with every keystroke.
Keyboard Format and Performance
The Enigma machine’s keyboard format was designed to facilitate simple typing and environment friendly encryption. The keys have been organized in a compact, QWERTY-style format, with every key equivalent to a selected letter or image. The operator would kind a message into the machine, and the keyboard would transmit {the electrical} alerts to the rotors, which might scramble the message accordingly. The plugboard additionally performed an important position within the encryption course of, because it launched further substitutions to the message.
The Enigma machine’s performance was centered across the rotor system, which consisted of three to 5 rotors, every with a special wiring sample. The rotors have been stacked on prime of one another, with the primary rotor on the left. Because the operator typed a message, {the electrical} alerts would circulation by way of the rotors, introducing further substitutions and rearrangements to the message. The plugboard would additionally modify the sign circulation by connecting sure letters to particular letters on the following rotor.
Comparability to Different Cryptographic Techniques
The Enigma machine’s encryption strategies have been unparalleled on the time, making it one of the vital safe communication programs on the planet. In comparison with different cryptographic programs of the period, the Enigma machine stood out for its advanced rotor system and plugboard, which launched a near-infinite variety of attainable encryption permutations. Different programs, such because the Hagelin cipher machine, relied on less complicated substitution tables and mechanical wheels, making them extra predictable and weak to cryptanalysis.
The Enigma machine’s encryption strategies have been additionally extra versatile and adaptable than different programs, permitting operators to simply change the settings and configurations to create new encryption patterns. This made the Enigma machine a pretty choice for safe communication, significantly for army and diplomatic functions.
The Enigma machine’s encryption strategies have been additional enhanced by means of encryption tables and key trade protocols. The German army used a fancy system of encryption tables and key trade protocols to make sure that the Enigma machine’s settings have been saved secret, even from different German brokers.
In abstract, the Enigma machine’s construction and operation have been designed to create a extremely safe encryption system that may shield German communications from interception and deciphering. Its distinctive keyboard format, plugboard, and rotor system made it one of the vital advanced and safe cryptographic gadgets of its time.
Polish Contributions and Early Breakthroughs
Marian Rejewski and his group in Poland made important contributions to the decryption of the Enigma machine, which laid the inspiration for the following breaking of the code by the British and the Individuals. The Polish group’s work was instrumental in deciphering the Enigma code, and their efforts paved the way in which for the Allied forces to achieve worthwhile intelligence throughout World Warfare II.
The Polish group’s insights into the Enigma machine have been gained by way of the usage of stolen machines, which they analyzed and experimented with to grasp its inside workings. They developed strategies for deducing the settings utilized by the machine, together with the usage of wheel patterns and plugboard connections.
Stolen Enigma Machines and Analytical Strategies
The Polish group obtained a number of Enigma machines by way of varied means, together with theft and buy. They then totally cleaned, repaired, and analyzed these machines to grasp their inside mechanics. Their analytical strategies allowed them to find out the machine’s settings, together with the wheel patterns and plugboard connections, which have been important for deciphering the encrypted messages.
-
The Polish group developed a system to establish the Enigma machine’s rotor order, which was important for understanding the machine’s inside workings.
In addition they created strategies for figuring out the wiring of the machine’s plugboards, which additional aided in deciphering the encrypted messages.
By finding out the machine’s inside workings, the Polish group was capable of create charts and tables to assist them decide the machine’s settings. -
The Polish group’s work additionally concerned the event of strategies for deducing the day by day settings utilized by the German operators, which included the usage of wheel patterns and plugboard connections.
In addition they created a system to establish the machine’s “key” for the day, which enabled them to decipher the encrypted messages.
The Polish group’s strategies for deducing the machine’s settings have been modern and efficient, they usually paved the way in which for the Allied forces to achieve worthwhile intelligence throughout World Warfare II.
“The Enigma machine was like a puzzle, and we needed to discover the lacking items to unravel it.”
— Marian Rejewski
The Polish group’s work laid the inspiration for the following breaking of the Enigma code by the British and the Individuals. Their analytical strategies and modern strategies for deciphering the Encrypted messages have been instrumental within the Allied forces’ final victory in World Warfare II.
British Codebreaking Efforts – Breaking the Malleable Machine
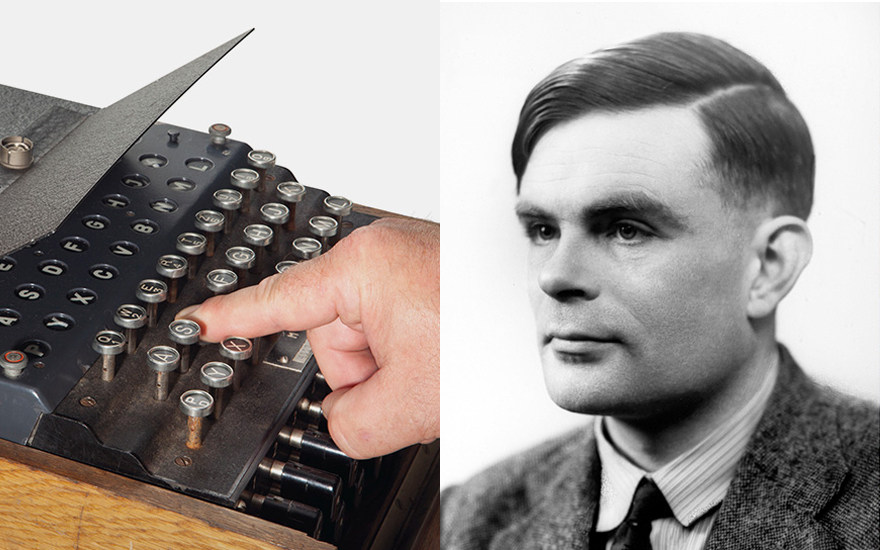
Alan Turing and his group on the Authorities Code and Cypher College (GC&CS) at Bletchley Park made important developments in cracking the Enigma code, which had been puzzling the British for a number of years. Their work marked a serious breakthrough within the warfare effort, permitting the Allies to achieve worthwhile intelligence on German army operations.
After the Polish cryptographers had recognized the Enigma machine’s working ideas and made preliminary headway in cracking its code, the British took over the duty with renewed vigor. Alan Turing, specifically, contributed considerably to the efforts, as did his colleague Gordon Welchman. They labored tirelessly to develop modern strategies to course of and analyze the huge quantities of encrypted messages intercepted by the British.
Machine Enhancements Impressed by Turing’s Work
Turing’s work led to a greater understanding of the Enigma machine’s internal workings and recognized areas the place its safety may very well be compromised. This newfound data immediately influenced the design of the Bombe, an electromechanical machine particularly created to decipher Enigma site visitors. The Bombe was an important addition to the British codebreaking efforts, permitting the group to course of messages at an unprecedented fee.
The Bombe was impressed by the Polish machine often called the ‘Rejewski’s Bomba’, and it tremendously enhanced the effectivity of codebreaking operations at Bletchley Park. Through the use of a sequence of electromechanical drums and levers, the Bombe simulated the Enigma machine’s encryption course of, permitting the group to infer the settings utilized by the Germans and subsequently crack the codes.
The enhancements made to the Enigma machine itself have been additionally knowledgeable by Turing’s analysis. His work highlighted the machine’s inherent malleability and the necessity for frequent adjustments to its settings to take care of its safety. This data was used to change the Enigma machine’s design, making it barely safer but in addition extra susceptible to errors that the British may exploit.
The Function of the Bombe in Codebreaking
The Bombe performed an important position within the British codebreaking efforts, processing and analyzing tens of millions of attainable settings to uncover the proper ones utilized by the Germans. This machine allowed the codebreakers to sort out the Enigma site visitors on a a lot bigger scale than ever earlier than, offering the Allies with a gradual circulation of high-quality intelligence.
-
The Bombe’s effectivity enabled the British to quickly course of Enigma messages, holding tempo with the Germans’ speedy adjustments to the machine’s settings. This allowed the codebreakers to constantly replace their data of the Enigma machine’s internal workings.
-
The Bombe additionally facilitated the event of extra refined analytical strategies, such because the “cribbing” technique, which concerned evaluating fragments of identified textual content to corresponding fragments of encrypted messages. This led to important breakthroughs in codebreaking.
The Bombe’s effectiveness was instrumental in sustaining the British codebreaking benefit all through the warfare. It supplied a strong basis for future developments in codebreaking, in the end contributing to the Allied victory.
The Bombe Machine and Codebreaking Effectivity
In 1939, Alan Turing and Gordon Welchman, two British mathematicians, designed and developed the Bombe machine on the Authorities Code and Cypher College (GC&CS) at Bletchley Park. The Bombe machine was a mechanical machine that considerably improved the effectivity of codebreaking by automating and rushing up the method of looking for the proper settings for the Enigma machine.
The Bombe machine was a big and complicated machine, consisting of a sequence of drums, electrical connections, and switches. It was powered by a sequence of motors and had a sequence of enter and output mechanisms. The machine used the same idea to the Enigma machine’s rotor system, with a number of drums and settings that may very well be adjusted to seek for the proper mixture of wheel order, ring setting, and plugboard connections.
The Mechanics of the Bombe Machine
The Bombe machine used a mixture of mechanical and electrical ideas to hurry up the codebreaking course of. It consisted of 5 drums, every representing one of many rotors within the Enigma machine. The drums have been linked by way of a sequence {of electrical} contacts, which have been used to seek for the proper mixture of rotor positions, rotor wiring, plugboard connections, and rotor ring settings.
How the Bombe Machine Labored
The Bombe machine labored by simulating the method of encrypting and decrypting a message with the Enigma machine. The operator would enter a sequence of letters and numbers into the machine, which might then seek for the proper settings that may outcome within the plaintext message being obtained. The machine would iterate by way of all attainable settings, utilizing a mixture of mechanical and electrical contacts to simulate the Enigma machine’s encryption course of.
Key Options of the Bombe Machine, How the enigma machine was cracked
Automated Search Mechanism
The Bombe machine’s automated search mechanism was its most vital innovation. It allowed the machine to look by way of all attainable settings in a fraction of the time it will take a human operator to take action. This made it attainable to crack the Enigma code in a matter of hours, somewhat than weeks or months.
Decreased Human Error
The Bombe machine additionally decreased human error, which was a major drawback in codebreaking. The machine’s mechanical and electrical contacts ensured that the settings have been entered appropriately, lowering the chance of human error.
Elevated Codebreaking Capability
The Bombe machine elevated codebreaking capability by permitting a number of operators to work on totally different elements of the codebreaking course of concurrently. This made it attainable to crack a number of Enigma messages in a brief interval.
Checklist of Key Improvements
- The Bombe machine’s automated search mechanism considerably improved codebreaking effectivity.
- The machine’s decreased human error fee ensured that settings have been entered appropriately, lowering the chance of error.
- The Bombe machine elevated codebreaking capability, permitting a number of operators to work on totally different elements of the codebreaking course of concurrently.
- The machine’s mechanical and electrical contacts simulated the Enigma machine’s encryption course of, making it attainable to crack the Enigma code.
- The Bombe machine performed an important position within the Allied victory in World Warfare II.
“The Bombe was a machine that might do the job of 20 or 30 males, and if it had been obtainable earlier, I consider that may have modified the entire course of the warfare.”
– Alan Turing
Human Computing and Statistical Strategies
Human computing and statistical strategies performed an important position within the codebreaking means of the Enigma machine. Mathematicians and statisticians used advanced algorithms and statistical strategies to decipher the cryptic messages, complementing the efforts of the Bombe machine and cryptanalysts. Their contributions have been instrumental in cracking the code, which considerably impacted the result of World Warfare II.
Human computer systems and statisticians have been accountable for analyzing and processing the huge quantity of knowledge generated by the Bombe machine. They employed statistical strategies to establish patterns and tendencies within the encrypted messages, which helped slim down the probabilities for the rotor settings and wheel orders. The group of human computer systems and statisticians labored tirelessly to course of the information, usually beneath intense strain and with restricted assets.
Statistical Strategies in Codebreaking
One important statistical technique used to crack the Enigma code was the “cribbing” method. Cribbing concerned figuring out a brief sequence of plaintext characters, often called a crib, that appeared within the encrypted message. By analyzing the frequency of letters and letter mixtures, the cryptanalysts may deduce the attainable location of the crib inside the encrypted message. This method relied closely on the statistical evaluation of letter frequencies, an idea developed by William Friedman, an American cryptanalyst, who studied the frequency distribution of letters within the English language. In response to
the Friedman frequency distribution
, the commonest letter within the English language is ‘E’, accounting for about 12.7% of all letters. By making use of this distribution to the encrypted message, the cryptanalysts may estimate the likelihood of every letter being in a specific place, thus rising the probabilities of figuring out the crib.
The “cribbing” method was used together with different statistical strategies, such because the
chi-squared check
, a statistical check used to find out whether or not the noticed frequencies of letters in an encrypted message differed considerably from the anticipated frequencies based mostly on the English language. By analyzing these frequencies, the cryptanalysts may establish patterns and tendencies that hinted on the presence of a crib.
Along with these statistical strategies, the human computer systems and statisticians performed an important position in processing the information generated by the Bombe machine. They used a mixture of psychological math and statistical software program to establish the attainable rotor settings and wheel orders, which considerably narrowed down the probabilities for the Enigma machine’s settings.
Statistical strategies corresponding to these, together with human computing and the Bombe machine, in the end contributed to the profitable cracking of the Enigma code, which had a profound impression on the result of World Warfare II.
Key Statistical Strategies
-
The Chi-Squared Take a look at
The chi-squared check was a statistical check used to find out whether or not the noticed frequencies of letters in an encrypted message differed considerably from the anticipated frequencies based mostly on the English language. By analyzing these frequencies, the cryptanalysts may establish patterns and tendencies that hinted on the presence of a crib.
-
Cribbing
The “cribbing” method concerned figuring out a brief sequence of plaintext characters, often called a crib, that appeared within the encrypted message. By analyzing the frequency of letters and letter mixtures, the cryptanalysts may deduce the attainable location of the crib inside the encrypted message.
-
Letter Frequencies
The cryptanalysts studied the frequency distribution of letters within the English language, which was developed by William Friedman. This distribution was used to investigate the likelihood of every letter being in a specific place within the encrypted message.
The Function of Intelligence and Human Error
The cracking of the Enigma code was a fancy course of that concerned a large number of things, together with intelligence networks and human error. Whereas the mathematical and logistical breakthroughs achieved by cryptanalysts and engineers are well-documented, it’s important to acknowledge the numerous contributions made by intelligence networks and human error.
Intelligence Networks
The British intelligence community performed an important position within the cracking of the Enigma code. By way of their community of brokers and spies, they obtained essential details about the Enigma machine and its working procedures. This data, mixed with the data gained from the Polish cryptanalysts, shaped the premise of the British codebreaking efforts. The British intelligence community was instrumental in gathering the mandatory information to grasp the machine’s mechanics and the encryption procedures utilized by the German army. This data allowed the British to construct on the work of the Polish cryptanalysts and make important breakthroughs in cracking the Enigma code.
- Probably the most important contribution of the British intelligence community was the seize of the Enigma machine from a German U-boat in 1941. This supplied the British with a working mannequin of the machine, which they used to develop the Bombe machine.
- The intelligence community additionally supplied details about the day by day keys and settings utilized by the German army to function the Enigma machine. This data allowed the British to grasp how the machine was being utilized in real-time, offering worthwhile insights into the enemy’s communication patterns.
Human Error
Human error performed a major position within the cracking of the Enigma code. The Enigma machine relied on the safety of a sequence of settings and keys being modified day by day. Nevertheless, human operators usually didn’t comply with procedures appropriately, which resulted in predictable patterns rising within the encrypted messages. The British codebreakers have been capable of exploit these patterns to make important breakthroughs in cracking the Enigma code.
- The German army had an inclination to make use of the identical keys for a number of messages, which created a predictable sample within the encrypted messages. This allowed the British codebreakers to establish the keys utilized in a specific message.
- The human error additionally included the truth that the German army usually transmitted redundant and redundant key messages, which have been simply intercepted by the British. The British codebreakers have been ready to make use of these intercepted messages to develop their very own keys for decrypting the Enigma machine.
Impression of Intelligence Networks and Human Error
The mixed impression of intelligence networks and human error was important. It allowed the British codebreakers to develop a deep understanding of the Enigma machine and its working procedures. This understanding enabled them to make important breakthroughs in cracking the Enigma code, offering invaluable intelligence to the Allies throughout World Warfare II.
Conclusion
The cracking of the Enigma code was a fancy course of that concerned a large number of things, together with intelligence networks and human error. Whereas the mathematical and logistical breakthroughs achieved by cryptanalysts and engineers are well-documented, it’s important to acknowledge the numerous contributions made by intelligence networks and human error. The mixed impression of those elements performed an important position within the success of the British codebreaking efforts and in the end contributed to the defeat of the German army in World Warfare II.
Key Takeaways
The important thing takeaways from the intelligence networks and human error are:
- The British intelligence community performed an important position within the cracking of the Enigma code by gathering details about the Enigma machine and its working procedures.
- Human error, corresponding to the usage of predictable patterns and redundant keys, allowed the British codebreakers to make important breakthroughs in cracking the Enigma code.
- The mixed impression of intelligence networks and human error was important, offering invaluable intelligence to the Allies throughout World Warfare II.
“The machine was not only a piece of {hardware}, however a system that relied on human operators to make sure its safety. The human error performed a major position within the cracking of the Enigma code.”
Legacy of Enigma Codebreaking: How The Enigma Machine Was Cracked

The Enigma codebreaking efforts, which came about from the Nineteen Twenties to the Nineteen Forties, had a profound impression on cryptographic historical past. The efforts of Polish cryptanalysts and British codebreakers, significantly Alan Turing and his group at Bletchley Park, demonstrated the significance of breaking advanced encryption programs. This legacy paved the way in which for contemporary cryptography, influencing the event of coding principle and the creation of safe communication programs.
The Impression on Cryptographic Historical past
The Enigma codebreaking efforts marked a major turning level within the historical past of cryptography. For the primary time, it demonstrated that advanced encryption programs may very well be damaged with the appropriate mixture of mathematical and computational strategies. This accomplishment had far-reaching penalties, resulting in a re-evaluation of cryptographic practices and the event of safer encryption strategies.
- The Enigma codebreaking efforts confirmed that encryption programs weren’t foolproof, resulting in a shift in direction of safer and versatile coding strategies.
- The event of the Bombe machine, a mechanical laptop designed to help in codebreaking, laid the inspiration for the creation of recent computer systems.
- The work of Alan Turing and his group at Bletchley Park supplied worthwhile insights into the significance of human computing and statistical strategies in codebreaking, highlighting the necessity for a multidisciplinary strategy to cryptography.
Classes Realized from the Enigma Codebreaking Undertaking
The Enigma codebreaking challenge taught a number of worthwhile classes that stay related to fashionable cryptography:
- The significance of collaboration and multidisciplinary approaches in codebreaking and cryptography.
- The necessity for a deep understanding of the underlying arithmetic and statistical ideas underlying encryption programs.
- The worth of human computing and statistical strategies in codebreaking, significantly in conditions the place computational assets are restricted.
- The significance of a versatile and adaptive strategy to cryptography, as encryption programs and strategies proceed to evolve.
The Relevance to Trendy Cryptography
The legacy of Enigma codebreaking continues to form fashionable cryptography, influencing the event of safe communication programs and coding principle. The Enigma codebreaking efforts demonstrated the significance of breaking advanced encryption programs, highlighting the necessity for a multidisciplinary strategy to cryptography. This data has been utilized in varied areas, together with:
“The machine has no thoughts, however it may be used to create a mannequin of the human thoughts,” – Alan Turing
- Pc safety: understanding the significance of human computing and statistical strategies in codebreaking has led to the event of safer encryption strategies and protocols.
- Coding principle: the Enigma codebreaking efforts led to a deeper understanding of the underlying arithmetic and statistical ideas underlying encryption programs, informing the event of recent coding principle.
- Synthetic intelligence: the work of Alan Turing and his group at Bletchley Park laid the inspiration for the event of synthetic intelligence and machine studying strategies, which are actually utilized in varied areas, together with cryptography and laptop safety.
- Cybersecurity: the Enigma codebreaking legacy continues to tell the event of safer and versatile coding strategies, highlighting the necessity for a multidisciplinary strategy to cryptography.
Closing Abstract
The Enigma codebreaking efforts, a major chapter in cryptographic historical past, exhibit the facility of collaboration, intelligence, and human ingenuity in overcoming seemingly insurmountable obstacles. The story of how the Enigma machine was cracked serves as a testomony to the significance of strategic considering, artistic problem-solving, and the unwavering dedication of people and groups in pursuit of an important objective.
Useful Solutions
Who was the primary particular person to crack the Enigma code?
Marian Rejewski, a Polish cryptographer, was the primary particular person to crack the Enigma code, alongside along with his colleagues Jerzy Różycki and Henryk Zygalski.
How did British cryptographers crack the Enigma code?
British cryptographers, led by Alan Turing and his group, made important developments in cracking the Enigma code, utilizing a mixture of mathematical and computational strategies, together with the event of the Bombe machine.
What was the importance of the Enigma codebreaking efforts?
The Enigma codebreaking efforts have been important as a result of they demonstrated the significance of cryptography in wartime communication and highlighted the significance of collaboration and modern problem-solving in overcoming advanced challenges.
How did the Enigma machine work?
The Enigma machine used a fancy sequence of rotors, wiring, and substitution tables to encrypt messages, producing a extremely safe encryption that was troublesome to decipher with out the proper key.