SSH into Home windows Machine units the stage for safe distant entry, providing readers a glimpse right into a story that’s wealthy intimately and authentic from the outset.
The world of distant computing has made our lives simpler, nevertheless it additionally raises issues about safety and reliability. On this article, we are going to stroll you thru the method of SSH right into a Home windows machine, discussing the fundamentals, preparation, and superior subjects.
SSH Fundamentals
SSH, or Safe Shell, is a safe protocol for distant entry to units over the web. Its goal is to supply a safe solution to entry and handle units remotely, with out compromising the safety of the machine or the community. That is notably necessary for units linked to the web, as they are often weak to unauthorized entry and assaults. Using SSH has change into widespread because of its ease of use, flexibility, and flexibility.
Distinction between SSH and different distant entry protocols
Whereas different distant entry protocols, comparable to Telnet, present a solution to entry units remotely, they don’t supply the identical degree of safety as SSH. SSH makes use of encryption to guard knowledge, together with passwords and instructions, from eavesdropping and tampering. This ensures that even when an attacker intercepts the connection, they will be unable to entry the info or instructions being transmitted.
SSH additionally differs from different protocols in its use of keys for authentication. SSH keys are a pair of digital keys used to authenticate customers and units, with out the necessity for passwords. That is safer than password-based authentication, as keys are generated and saved securely, and the danger of key guessing or brute-force assaults is considerably diminished.
Significance of SSH keys in safe distant entry
SSH keys are a vital a part of safe distant entry utilizing SSH. Keys are generated utilizing algorithms, comparable to RSA or DSA, and encompass a personal key and a public key. The non-public key’s saved securely on the client-side, whereas the general public key’s saved on the server-side. This enables the consumer to authenticate itself to the server with out the necessity for a password.
SSH keys are safer than passwords in a number of methods:
*
- Passwords could be simply guessed or cracked utilizing brute-force assaults, whereas ssh keys are nearly unguessable.
- Passwords could be stolen or intercepted, whereas safe ssh keys are generated and saved securely.
- Passwords could be compromised because of weak password insurance policies, whereas ssh keys are immune to password-related safety points.
SSH key advantages embrace:
- Quick and dependable connections: SSH keys enable for quick and dependable connections between units, with out the necessity for password authentication.
- Improved safety: SSH keys are safer than passwords, lowering the danger of unauthorized entry and assaults.
- Straightforward to make use of: SSH keys are simple to make use of, without having to recollect complicated passwords or usernames.
SSH is extensively used and supported:
SSH is extensively supported by most working techniques, together with Home windows, Linux, and macOS, making it simply accessible and usable.
Selecting an SSH Shopper
In relation to accessing your Home windows machine by way of SSH, you will want to pick out an appropriate SSH consumer. This resolution is essential as it’ll affect your total safety, compatibility, and consumer expertise. There are a number of fashionable SSH purchasers obtainable for Home windows, every with its personal strengths and weaknesses.
Standard SSH Shoppers for Home windows
Among the most well-known SSH purchasers for Home windows embrace:
PuTTY is usually thought-about the gold customary for SSH purchasers on Home windows, with a big consumer base and intensive function set.
-
PuTTY
PuTTY is a well-liked open-source SSH consumer for Home windows, providing superior options comparable to a number of session help, public key authentication, and help for numerous community protocols.
- PuTTY is a good choice for customers who require superior SSH options and customization choices.
- Nevertheless, because of its complexity and steep studying curve, PuTTY might not be excellent for inexperienced persons or customers preferring a extra easy expertise.
-
OpenSSH
OpenSSH is one other extensively used SSH consumer for Home windows, providing strong security measures, a user-friendly interface, and compatibility with numerous platforms.
- OpenSSH gives safe connections, with options comparable to key-based authentication, encryption protocols, and safe knowledge transmission.
- OpenSSH additionally helps numerous protocols, together with SSHv1, SSHv2, and SFTP, making it suitable with a variety of techniques.
-
Home windows Subsystem for Linux (WSL)
WSL permits customers to run a Linux setting natively inside Home windows 10, providing a seamless integration of Linux instruments and instructions with Home windows.
- WSL eliminates the necessity for separate SSH purchasers, as customers can merely use the native Linux instruments and instructions throughout the Home windows setting.
- This makes WSL a beautiful choice for builders, energy customers, and directors who rely closely on Linux instruments and workflows.
- Complexity: Some SSH purchasers, like PuTTY, supply a variety of superior options, which could be useful for energy customers however overwhelming for inexperienced persons.
- Safety Options: As with every security-related device, it is important to contemplate the extent of safety provided by the SSH consumer, together with options comparable to encryption protocols and key-based authentication.
- Compatibility: Be certain that the chosen SSH consumer helps the required protocols and is suitable along with your goal techniques.
- Person Interface: Take into account the consumer expertise and interface of the SSH consumer, as this may considerably affect your productiveness and total satisfaction.
- Upon preliminary login, the consumer copies the general public key to their host machine, which then makes use of this key to confirm the consumer’s non-public key, guaranteeing licensed entry.
- After the preliminary setup, when the consumer makes an attempt to log in, their consumer utility encrypts a session ID with their non-public key, transmitting the encrypted session ID to the server.
- The server decrypts this ID with the saved public key, if it matches the saved public key, the consumer’s id is confirmed.
- CA-signed certificates: These certificates are issued by a trusted CA and comprise the consumer’s public key and id data.
- Shopper-certificates: These certificates are utilized by purchasers to authenticate with an SSH server.
- Password insurance policies: SSH servers could be configured to implement complicated password insurance policies, comparable to minimal password size and complexity necessities.
- Password rotation: Common password rotation may help forestall password compromise, making it tougher for attackers to achieve entry to the system.
- Password authentication protocols: SSH servers could be configured to make use of stronger password authentication protocols, comparable to password authentication protocol (PAP) or problem handshake authentication protocol (CHAP).
- Public key algorithms: SSH servers could be configured to make use of numerous public key algorithms, comparable to RSA or elliptic curve cryptography (ECC).
- Personal key administration: SSH purchasers must handle their non-public keys securely, utilizing strategies comparable to encrypted storage and safe password administration.
- DH key alternate: This algorithm is extensively utilized in SSH connections and gives a excessive degree of safety.
- ECDH key alternate: This algorithm is safer than DH and gives a better degree of safety.
- To make use of SSH classes with distant desktop or VPS connections, merely save the connection particulars as a session in your SSH consumer.
- Subsequent, whenever you hook up with the distant setting, use the SSH consumer to log in to the distant server or desktop.
- As soon as linked, you should utilize the distant desktop or VPS to entry your information, functions, and assets, simply as you’ll on a neighborhood machine.
- To make use of SSH classes for background processes, first save the connection particulars as a session in your SSH consumer.
- Subsequent, create a script or command that you simply need to run within the background, and add it to the distant server.
- Utilizing the SSH consumer, hook up with the distant server and use the `ssh-agent` command to run the script or command within the background.
- Incorrect Credentials: Double-check your SSH consumer configuration, username, and password or non-public key. Be certain that the SSH server is configured to make use of the identical authentication technique (e.g., username/password or public key).
- Incorrect Personal Key: Confirm that you simply’re utilizing the proper non-public key pair, and the non-public key’s correctly configured on the client-side.
- SSH Server Configuration: Test the SSH server configuration to make sure it is set as much as enable public key authentication and that the authorized_keys file is accurately configured.
- Permissions Points: Be certain that the SSH daemon has the proper permissions to entry the non-public key and authorized_keys file.
- Community Congestion: Test the community congestion and be certain that the community connections are secure. You need to use instruments like `iperf` or `tcpdump` to diagnose community points.
- Firewall Guidelines: Confirm that the firewalls and entry management lists (ACLs) usually are not blocking SSH site visitors. Be certain that the SSH server is configured to permit incoming connections on the proper port.
- DNS Decision Points: Test the DNS decision of the SSH server’s hostname or IP deal with. You need to use instruments like `dig` or `nslookup` to diagnose DNS decision issues.
- SSH Server Port: Be certain that the SSH server is listening on the proper port (customary SSH port is 22).
- SSH Server Availability: Use instruments like `ssh` or `ssh -o` to confirm the server’s availability and test if it is responsive.
- Log Recordsdata: Test the SSH server’s log information (e.g., `/var/log/auth.log` or `/var/log/safe`) for any error messages or clues which will point out what’s inflicting the problem.
- System Sources: Confirm that the SSH server has the required system assets, comparable to CPU, reminiscence, and disk area.
- ssh -v: Use the `-v` choice with `ssh` to allow verbose mode and get detailed details about the SSH connection course of.
- ssh -vv: Use the `-vv` choice to get much more detailed details about the SSH connection course of.
- ssh -vvv: Use the `-vvv` choice to get essentially the most detailed details about the SSH connection course of.
- SFTP is predicated on the FTP (File Switch Protocol) protocol however makes use of SSH for authentication and encryption. It gives a high-level API for interacting with distant file techniques.
- SCP, then again, is an easy protocol that means that you can switch information securely utilizing SSH.
- The `sftp` command is used to entry an SFTP server, whereas `scp` is used to switch information between two native or distant hosts.
- For instance, to switch a file out of your native machine to a distant machine utilizing SCP, you’ll use the command: `scp local_file.txt consumer@remote_host:remote_directory/`
- SSH tunneling works by establishing a safe connection between the 2 hosts after which forwarding site visitors from one host to the opposite.
- The `ssh` command can be utilized to create a tunnel, which can be utilized to ahead site visitors from a distant host to a neighborhood host, and vice versa.
- For instance, to create an SSH tunnel out of your native machine to a distant host, you’ll use the command: `ssh -L 8080:localhost:80 consumer@remote_host`
- Port forwarding means that you can ahead site visitors from a selected port on the native host to a special port on the distant host.
- The `ssh` command can be utilized to ahead site visitors from a distant host to a neighborhood host, and vice versa.
- For instance, to ahead site visitors from port 80 on the native host to port 8080 on the distant host, you’ll use the command: `ssh -L 8080:localhost:80 consumer@remote_host`
Components Influencing the Selection of SSH Shopper
A number of elements ought to be thought-about when choosing an SSH consumer, together with:
Putting in and Configuring the Chosen SSH Shopper
As soon as you’ve got chosen the acceptable SSH consumer, the set up and configuration course of varies relying on the chosen device. For instance:
* To put in PuTTY, merely obtain and run the installer.
* For OpenSSH, you will want to put in the Home windows Subsystem for Linux (WSL), which incorporates OpenSSH.
* WSL is pre-installed with Home windows 10, making it simply accessible.
Please be aware that this isn’t an exhaustive information and it’s endorsed to seek the advice of the official documentation for every SSH consumer for extra detailed set up and configuration directions.
SSH Connection Strategies
SSH connections depend on safe authentication and key alternate processes to make sure knowledge integrity. On this context, we’ll delve into the elemental connection strategies.
In SSH, two main strategies for establishing connections can be found:
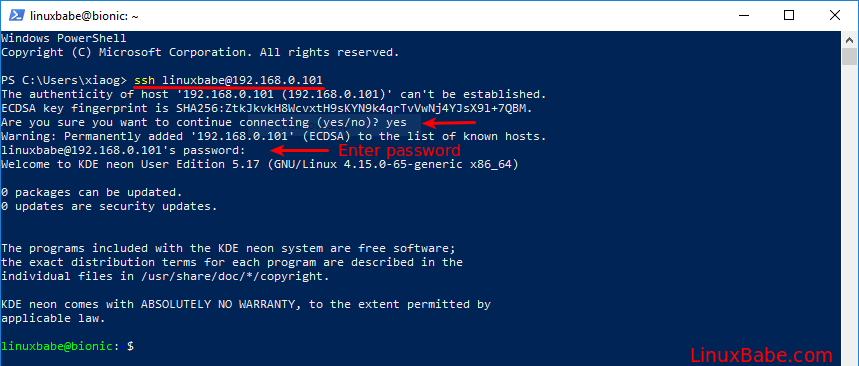
SSH Password Authentication
SSH password authentication is essentially the most easy technique, the place the consumer sends a username and password to the server for verification. This technique includes three foremost steps:
–
The Handshake
The SSH handshake is the preliminary connection institution, the place the consumer initiates communication with the server. The method includes negotiating protocol variations and algorithms for encryption and key alternate.
–
Key Change
Key alternate is a basic side of SSH connections. On this course of, either side negotiate a shared secret key to facilitate safe communication. Key alternate could be achieved utilizing algorithms like Diffie-Hellman or Elliptic Curve Diffie-Hellman.
–
Authentication
Authentication is the ultimate step within the SSH connection course of. Upon profitable key alternate, the consumer and server have interaction in a technique of mutual authentication, guaranteeing each events agree on the id and permissions of the consumer.
Moreover SSH password authentication, there are different key alternate and authentication strategies, like public key authentication. This technique depends on private and non-private key pairs to determine safe connections. When public key authentication is used, the consumer gives the server with a public key, which the server verifies towards a domestically saved non-public key.
Nevertheless, for customers unfamiliar with public key authentication, password authentication affords a better, albeit less-secure preliminary entry into SSH connections.
A special technique can also be obtainable,
SSH public key authentication
Public key authentication depends on the RSA or DSA (Digital Signature Algorithm) algorithms to create a pair of keys: a public key and a personal key.
One other connection technique is SFTP (Safe File Switch Protocol), which, though associated to SSH, has some key variations from SSH connections.
SSH and SFTP connections
SSH focuses on safe distant entry and command-line execution, whereas SFTP is particularly tailor-made for file transfers. Whereas SFTP connections could be established utilizing SSH protocols, they serve distinct functions.
A basic side distinguishing SSH and SFTP is the protocol’s core performance:
– SSH establishes a channel for executing distant instructions and executing native information or executing distant information.
– SFTP transfers knowledge over a Safe Shell session.
Distinction in key alternate and authentication
Though each SSH and SFTP share the same authentication mechanism, SSH focuses on authenticating customers for command execution and file entry, whereas SFTP emphasizes safe knowledge switch.
Abstract of the SSH connection course of
To recap the important thing facets of an SSH connection:
– The consumer begins with a handshake.
– Subsequent, they set up a shared secret key by means of key alternate.
– Lastly, each events endure a technique of mutual authentication, verifying the consumer’s id.
Distinction between SSH and SFTP
Though they coexist, SSH and SFTP connections fulfill completely different functions:
– SSH gives safe distant entry and command execution.
– SFTP is particularly designed for safe file switch.
Securing SSH Connections
Safe SSH connections are essential for safeguarding delicate knowledge and stopping unauthorized entry to your techniques. To realize this, you could implement strong safety measures, together with using certificates, passwords, and public key authentication.
Certificates-Based mostly Authentication
Certificates-based authentication is a extensively used technique for securing SSH connections. On this method, an SSH consumer makes use of a certificates supplied by a trusted certification authority (CA) to authenticate with an SSH server. This technique gives a excessive degree of safety, because the consumer’s id is verified earlier than accessing the server.
Certificates-based authentication is especially helpful in environments the place a excessive degree of safety is required, comparable to in monetary establishments or authorities businesses.
Password-Based mostly Authentication
Password-based authentication is an easy and extensively used technique for securing SSH connections. On this method, the SSH consumer is prompted to enter a password to entry the SSH server. This technique is simple to implement however might not be as safe as different strategies, as passwords could be compromised by means of numerous means.
Whereas password-based authentication gives a fundamental degree of safety, it’s important to implement extra safety measures, comparable to public key authentication, to reinforce total safety.
Public Key Authentication
Public key authentication is a extremely safe technique for securing SSH connections. On this method, the SSH server makes use of a pair of keys, one public and one non-public, to authenticate the consumer. This technique gives a excessive degree of safety, because the consumer’s id is verified utilizing the general public key.
Public key authentication is especially helpful in environments the place a excessive degree of safety is required, comparable to in monetary establishments or authorities businesses.
SSH Encryption
SSH encryption is essential for safeguarding delicate knowledge transmitted between an SSH consumer and server. SSH encryption strategies, comparable to AES (Superior Encryption Normal) and Blowfish, present a excessive degree of safety, making it tough for attackers to intercept or compromise the info.
The encryption key’s derived from the important thing alternate algorithm and the authentication technique used.
Key Change Algorithms
Key alternate algorithms are used to barter a shared secret key between an SSH consumer and server. Key alternate algorithms, comparable to Diffie-Hellman (DH) and elliptic curve Diffie-Hellman (ECDH), present a excessive degree of safety, making it tough for attackers to compromise the shared secret key.
In conclusion, securing SSH connections requires the implementation of strong safety measures, together with certificate-based, password-based, and public key authentication, in addition to SSH encryption and key alternate algorithms.
Managing SSH Periods
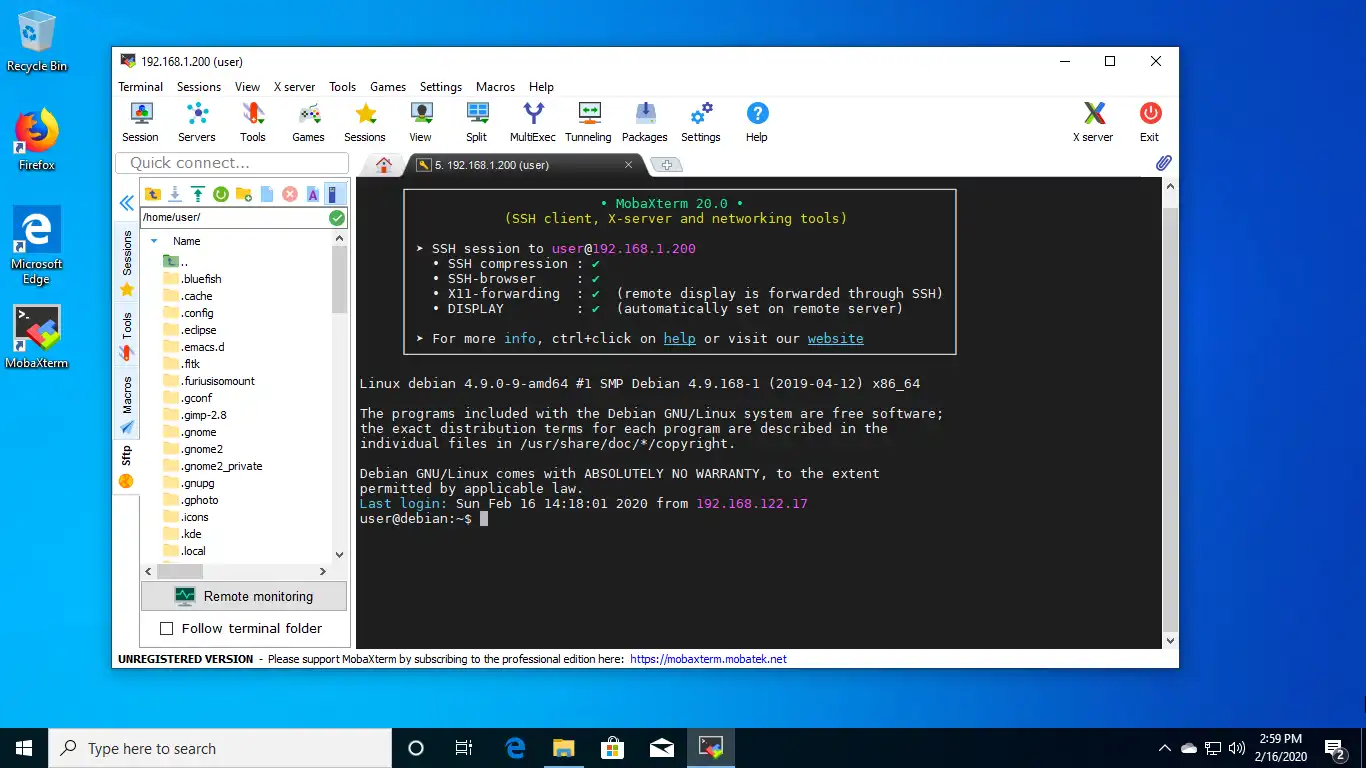
Managing a number of SSH connections could be a daunting process, however fortuitously, many SSH purchasers present options to simplify the method. With the power to open tabs, classes, and background connections, you may effectively handle a number of connections and cut back the danger of unintentional disconnections or misplaced work.
Managing A number of SSH Connections
Most SSH purchasers assist you to open a number of connections in tabs or separate home windows. This function is very helpful if you could work with a number of servers or initiatives concurrently. By opening every connection in a separate tab, you may simply change between them and keep away from cluttering your display screen with a number of home windows.
SSH purchasers like PuTTY, SSH Terminal, and iTerm2 supply tab administration options, permitting you to simply change between connections and handle a number of tabs.
To benefit from this function, merely right-click (or Ctrl-click on Mac) on a tab and choose “New Tab” or use the keyboard shortcut to open a brand new tab. You can too use the “Periods” function to save lots of ceaselessly used connections and simply recall them later.
Utilizing SSH Periods with Distant Desktop or VPS (Digital Personal Server) Connections
SSH classes can be utilized with distant desktop or VPS connections to supply an extra layer of safety and suppleness. By utilizing SSH to connect with a distant desktop or VPS, you may be certain that your connection is encrypted and safe, even should you’re accessing the distant setting over a public community.
Advantages of Utilizing SSH Periods for Background Processes
SSH classes can be used to run background processes, comparable to scheduled duties or steady integration workflows. By utilizing SSH to connect with a distant server, you may run scripts or instructions within the background, liberating up your native machine’s assets and guaranteeing that your processes run easily and effectively.
The `ssh-agent` command means that you can run SSH connections within the background, liberating up your native machine’s assets and guaranteeing that your processes run easily and effectively.
Troubleshooting SSH Points

Troubleshooting SSH points could be irritating, particularly when a connection hangs or authentication fails. Don’t be concerned! We have got you coated. On this part, we’ll stroll you thru widespread SSH connection points, strategies for resolving them, and finest practices for troubleshooting SSH connections.
Authentication Failures
Authentication failures are probably the most widespread SSH points. They happen when the consumer and server can not confirm one another’s identities. This may result in failed login makes an attempt and frustration. To resolve authentication failures, we have to have a look at the next:
Community Connectivity Issues, Ssh into home windows machine
Community connectivity issues are one other widespread subject when troubleshooting SSH connections. These points can come up because of numerous causes, comparable to community congestion, firewall guidelines, or DNS decision issues.
Checking Server Standing
Earlier than diving into troubleshooting SSH points, it is important to test the server standing. This contains verifying the SSH server’s availability, checking its log information, and guaranteeing that the server has the required system assets.
Utilizing SSH Debugging Instruments
SSH debugging instruments may help you establish and resolve SSH connection points. These instruments present detailed details about the SSH connection course of and may help you pinpoint the basis explanation for the issue.
Superior SSH Subjects on Home windows Machine: Ssh Into Home windows Machine
SSH is a robust protocol for safe distant entry and communication. Along with easy SSH connections, there are a number of superior subjects that may show you how to make the most of SSH to its full potential on a Home windows machine.
SSH File Switch and Synchronization
SSH file switch and synchronization are important for a lot of use instances, comparable to knowledge switch, backup, and automation. There are two main methods to switch information utilizing SSH: SFTP (Safe File Switch Protocol) and SCP (Safe Copy).
SSH Tunneling for Safe Communication
SSH tunneling means that you can create a safe connection between two hosts by forwarding community site visitors by means of an SSH connection. That is helpful for accessing assets which can be solely obtainable on the native community, comparable to web sites or companies.
SSH Port Forwarding and Redirection
SSH port forwarding and redirection are associated to SSH tunneling however are extra targeted on forwarding particular ports and redirecting site visitors.
Closing Abstract
In conclusion, SSH right into a Home windows machine is a robust device for safe distant entry. By following the steps Artikeld on this article, you may arrange a safe connection and luxuriate in the advantages of distant computing.
Question Decision
Q: What’s SSH and why do I want it?
A: SSH, or Safe Shell, is a safe protocol that means that you can entry a distant machine securely over the web. You want it for safe distant entry and file switch.
Q: What’s the distinction between SSH and SFTP?
A: SSH is a safe protocol for distant entry, whereas SFTP (Safe File Switch Protocol) is a protocol for safe file switch.
Q: How do I safe my SSH connection?
A: You’ll be able to safe your SSH connection through the use of public key authentication, certificates, and powerful passwords.