This Construct of Vanguard Can’t Run on Untrusted Machines, so you will not have the ability to play it on public computer systems or your mates’ outdated laptops. Vanguard is a sport that requires an excellent safe surroundings to run easily, and your mates’ computer systems are in all probability not reliable.
On this article, we’ll clarify why Vanguard cannot run on untrusted machines, the dangers of taking part in it on public computer systems, and how one can hold your account secure.
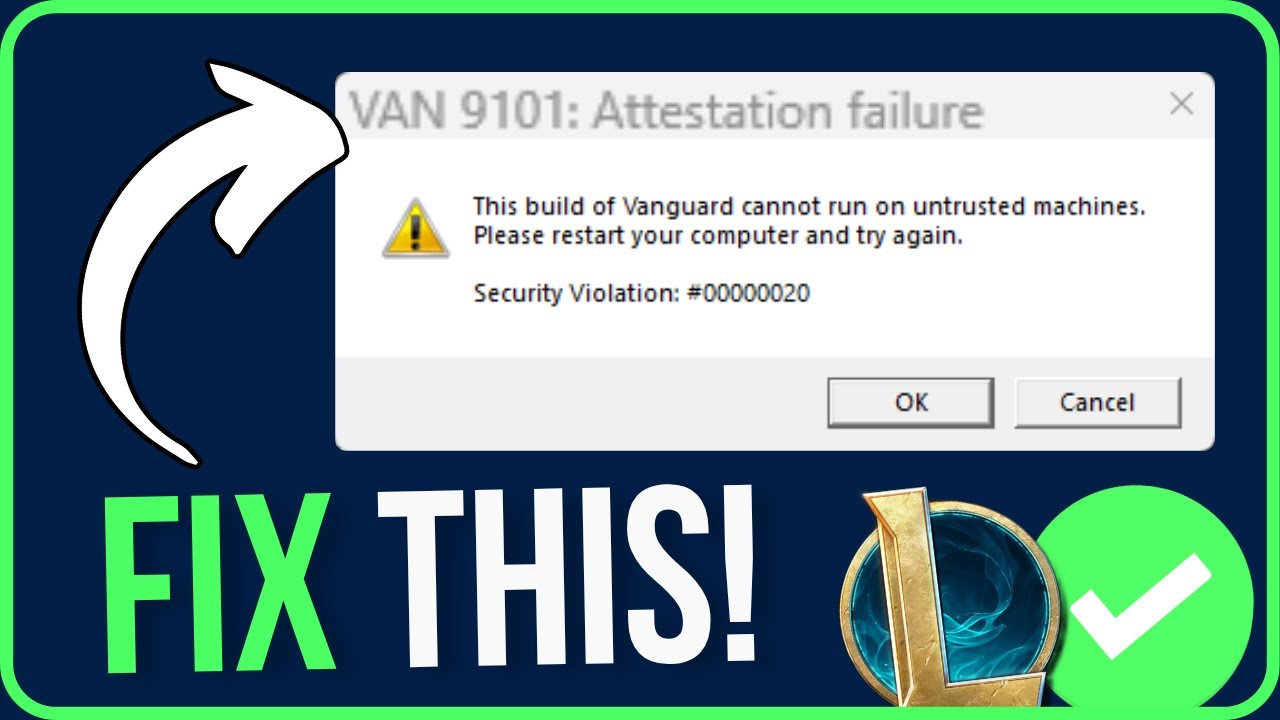
Understanding the Error Message
This error message signifies that the present construct of Vanguard can’t be executed on a machine whose safety stage is taken into account untrusted. Vanguard is a digital title that depends closely on on-line authentication and validation to operate correctly, making it extremely vulnerable to safety threats. When Vanguard detects that it is operating on an untrusted machine, it refuses to launch as a precautionary measure to guard the sport and its customers from potential safety dangers.
Causes for this Error
When Vanguard detects that it is operating on an untrusted machine, it usually outcomes from one in all a number of causes:
The machine is operating on an working system that isn’t formally supported by the sport.
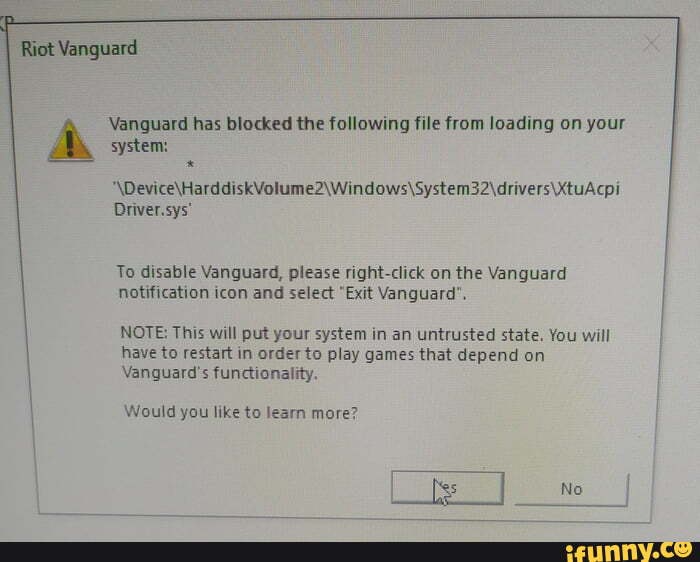
The machine’s safety settings are configured to dam the sport from operating.
The sport’s authenticity couldn’t be verified attributable to a lacking or corrupted configuration file.
Working techniques not formally supported by the sport could pose safety dangers to Vanguard and its customers. All the time guarantee your working system is up-to-date and operating a supported model.
Dangers of Operating Vanguard on Untrusted Machines
Operating Vanguard on an untrusted machine exposes the sport and its customers to the next dangers:
Malware infections: Untrusted machines could have malware that may inject malicious code into the sport, compromising its safety and probably stealing consumer knowledge.
Knowledge tampering: Malicious actors could try to change sport knowledge or information on an untrusted machine, disrupting the consumer’s expertise and probably resulting in account bans.
- Malicious actors could inject malware into the sport that may steal consumer credentials or delicate info.
- Customers could inadvertently obtain malware by operating Vanguard on an untrusted machine, which might compromise their complete laptop system.
Examples of Conditions The place this Error Might Happen, This construct of vanguard can not run on untrusted machines
The next situations could lead to Vanguard being unable to run on an untrusted machine:
A consumer’s laptop is related to a public Wi-Fi community and Vanguard is trying to authenticate on-line.
A consumer is operating Vanguard on a digital machine or a cloud-based working system that isn’t formally supported by the sport.
A consumer has a compromised or outdated working system that Vanguard’s safety measures detect as a possible risk.
A consumer’s safety software program or firewall settings block Vanguard’s skill to connect with the web servers attributable to a false optimistic or misconfigured rule.
Safety Necessities of Vanguard
Securely implementing Vanguard on trusted machines is essential for a seamless and guarded expertise. The necessities for safety differ considerably between trusted and untrusted machines, as Vanguard employs stringent safety protocols to safeguard delicate info and performance.
One important facet of Vanguard’s safety is its reliance on trusted machines. These machines should meet particular safety necessities, which embrace:
Vanguard’s Safety Necessities for Trusted Machines
To ascertain a safe reference to Vanguard, trusted machines should meet the next standards:
- The machine must be operating on a model of the working system that’s appropriate with Vanguard.
- The machine ought to have up-to-date safety patches and updates put in to forestall any potential vulnerabilities from being exploited.
- The machine must be configured with a safe browser, able to dealing with delicate info and safe connections.
- The machine ought to have a dependable and safe community connection, free from malware and different safety threats.
Vanguard’s safety measures are designed to guard delicate info from unauthorized entry. Nonetheless, if a trusted machine fails to fulfill these safety necessities, the implications will be extreme, together with knowledge breaches, system compromise, and unauthorized entry. These penalties spotlight the significance of adhering to safety necessities for trusted machines.
The distinction between Vanguard’s safety measures for trusted and untrusted machines lies within the stage of verification and validation. Trusted machines endure rigorous verification and validation to make sure their safety, whereas untrusted machines depend on extra primary safety protocols. This distinction is crucial in sustaining the integrity of Vanguard’s performance and knowledge safety.
To grasp the affect of not assembly safety necessities for Vanguard, think about the potential penalties of knowledge breaches or system compromise on the group or particular person utilizing Vanguard. These penalties embrace monetary losses, reputational harm, and even authorized liabilities.
Vanguard’s safety necessities and protocols are designed to forestall these penalties by guaranteeing the integrity of delicate info and performance. By adhering to those necessities, trusted machines can securely work together with Vanguard, safeguarding the confidentiality, integrity, and availability of delicate info.
In Vanguard, encryption is used to guard knowledge in transit and at relaxation. The system employs end-to-end encryption to make sure that knowledge is just accessible to approved events, including a further layer of safety.
Confidentiality, Integrity, and Availability (CIA) are the three main safety rules in Vanguard.
The system’s safety structure ensures that entry to delicate info and performance is restricted to approved customers and machines, thereby stopping unauthorized entry, malicious actions, and different safety threats.
For trusted machines to securely work together with Vanguard, they have to meet the safety necessities talked about earlier, together with up-to-date safety patches, a safe browser, and a dependable community connection.
In abstract, Vanguard’s safety necessities and protocols are designed to guard delicate info and performance from unauthorized entry, malicious actions, and different safety threats. By adhering to those necessities, trusted machines can securely work together with Vanguard, safeguarding confidentiality, integrity, and availability.
Trusted Machine Necessities
To make sure a safe surroundings for Vanguard software program, a machine should meet particular system necessities. A trusted machine is one which has been correctly configured to keep away from potential safety dangers and preserve the integrity of the software program.
Minimal System Necessities
A machine should meet the next minimal system necessities to be thought-about trusted:
- The working system must be up-to-date, with the newest service pack put in.
- The {hardware} must be able to performing effectively with the software program, with a minimal of 8 GB of RAM and a 2.4 GHz processor.
- A steady web connection of no less than 1 Mbps, and a dependable energy supply are additionally important.
A steady and well-configured machine ensures that the Vanguard software program runs easily and effectively, whereas additionally sustaining optimum efficiency.
Up-to-Date Working System and Software program Installations
An up-to-date working system and software program installations are essential for sustaining a trusted surroundings. A well-configured working system helps forestall safety vulnerabilities, whereas additionally guaranteeing optimum efficiency.
Patches and updates must be put in often to keep away from potential safety dangers.
A well-maintained machine additionally helps forestall software program incompatibilities and efficiency points.
Antivirus Software program and Firewalls
A good antivirus software program and a powerful firewall are important elements of a trusted machine. Antivirus software program helps defend in opposition to malware, ransomware, and different sorts of cyber threats, whereas a firewall prevents unauthorized entry to the machine and its knowledge.
A good antivirus software program must be put in on the machine always.
A powerful firewall helps forestall unauthorized entry to the machine and its knowledge, thereby guaranteeing the safety and integrity of the Vanguard software program.
The significance of antivirus software program and firewalls can’t be overstated, as they supply a crucial layer of safety in opposition to numerous sorts of cyber threats.
Greatest Practices for Sustaining Trusted Machines: This Construct Of Vanguard Can’t Run On Untrusted Machines

Sustaining a trusted machine surroundings is essential for guaranteeing the safety and integrity of delicate knowledge, notably in environments the place knowledge safety and compliance are crucial, resembling in finance, healthcare, and authorities sectors. A trusted machine surroundings ensures that machines are free from malware, viruses, and different malicious software program that might compromise the confidentiality, integrity, and availability of delicate knowledge.
Implementing Robust Entry Controls
Entry controls are crucial in stopping unauthorized entry to machines, networks, and knowledge. Implementing robust entry controls, resembling multi-factor authentication, role-based entry management, and least privilege entry, helps to make sure that solely approved personnel have entry to machines and delicate knowledge.
- Multifactor authentication provides a further layer of safety, making it tougher for attackers to realize unauthorized entry to machines and knowledge.
- Position-based entry management ensures that customers are granted entry to assets primarily based on their job capabilities and duties.
- Least privilege entry restricts customers to solely the privileges they should carry out their job capabilities, decreasing the chance of knowledge breaches and unauthorized entry.
Many organizations, such because the US Division of Protection and the Nationwide Safety Company (NSA), implement robust entry controls as a greatest follow for sustaining a trusted machine surroundings.
Retaining Software program Up-to-Date
Retaining software program up-to-date is crucial in sustaining a trusted machine surroundings. Outdated software program could comprise recognized vulnerabilities that may be exploited by attackers to realize unauthorized entry to machines and knowledge. Implementing common software program updates and patches helps to make sure that machines are protected against recognized vulnerabilities.
- Common software program updates and patches assist to deal with recognized vulnerabilities and stop assaults.
- Outdated software program could comprise recognized vulnerabilities that may be exploited by attackers to realize unauthorized entry to machines and knowledge.
- Sustaining a patch administration system helps to make sure that all software program is up-to-date and patched, decreasing the chance of knowledge breaches and unauthorized entry.
Examples of firms which have applied common software program updates and patches embrace Google, Microsoft, and Amazon Net Providers (AWS). These firms often replace their software program to deal with recognized vulnerabilities and make sure the safety and integrity of their machines and knowledge.
Usually Monitoring Machines and Networks
Usually monitoring machines and networks helps to detect and reply to potential safety threats in real-time. Implementing a risk detection system, resembling intrusion detection and prevention techniques (IDPS) and safety info and occasion administration (SIEM) techniques, helps to establish potential safety threats and stop assaults.
- Usually monitoring machines and networks helps to detect and reply to potential safety threats in real-time.
- IDPS and SIEM techniques assist to establish potential safety threats and stop assaults.
- A risk detection system helps to establish and reply to safety threats, decreasing the chance of knowledge breaches and unauthorized entry.
Examples of firms which have applied common monitoring and risk detection techniques embrace JPMorgan Chase, Financial institution of America, and Citigroup. These firms often monitor their machines and networks to detect and reply to potential safety threats.
Final Recap
In conclusion, taking part in Vanguard on untrusted machines is a giant no-no. To remain secure, make certain to play it on a pc you management, and all the time hold your software program updated.
Questions Typically Requested
Q: What are untrusted machines?
A: Untrusted machines are computer systems that aren’t safe, both as a result of they’re outdated, have malware, or have been hacked.