Delving into copy gpg keys from different machine utilizing scp, this introduction immerses readers in a singular and compelling narrative. Safe communication performs a significant function in at this time’s digital panorama.
The idea of GPG keys, their goal, and eventualities the place copying GPG keys from one machine to a different is important set the inspiration for understanding the significance of GPG key administration. As well as, the SCP protocol is a widely-used technique for securely transferring recordsdata between servers.
Introduction to Copying GPG Keys with SCP: Copy Gpg Keys From Different Machine Utilizing Scp
Within the digital age, safe communication is extra essential than ever. GPG keys play a significant function on this course of, making certain that our digital messages stay encrypted and protected against prying eyes. However what precisely are GPG keys, and why do we have to copy them from one machine to a different?
GPG keys, quick for GNU Privateness Guard keys, are pairs of cryptographic keys used for encryption and decryption. They’re the spine of safe communication, permitting people and organizations to ship and obtain delicate info with confidence. Think about a locked field, the place solely the particular person with the corresponding key can unlock it. That is the idea behind GPG keys.
When we have to ship or obtain delicate info, similar to emails or recordsdata, we use our GPG keys to encrypt and decrypt the information. This ensures that even when the knowledge is intercepted, it stays unreadable with out the corresponding key.
So, when do we have to copy GPG keys from one machine to a different? There are a number of eventualities the place this turns into needed:
* Machine migration: When switching from an previous machine to a brand new one, we have to switch our GPG keys to make sure continuity in safe communication.
* Collaboration: When working with a crew or group, we might have to share our GPG keys to allow safe communication and collaboration.
* Backup: In case of information loss or system failure, copying our GPG keys ensures that we will get better our encryption capabilities.
Now, let’s dive into the world of SCP, the protocol used for copying GPG keys from one machine to a different.
SCP Protocol Overview
SCP, or Safe CoPy, is a protocol designed for safe information switch. It makes use of cryptography to make sure that the information transferred is genuine and never tampered with throughout transmission. SCP is commonly utilized in conditions the place information must be transferred securely over a community.
SCP works by establishing a safe connection between the sender and receiver, utilizing public-key cryptography to authenticate the sender’s id. As soon as the connection is established, the sender can ship the GPG keys to the receiver.
SCP is broadly used within the Linux and Unix world, and can be out there on Home windows. Its excessive security measures make it a really perfect selection for transferring delicate information, together with GPG keys.
Comparability of GPG Key Administration Strategies, Copy gpg keys from different machine utilizing scp
GPG keys are an important a part of safe communication. However how will we handle them successfully? This is a comparability of various GPG key administration strategies:
| Technique | Description |
|---|---|
| GPG Keys | Safe encryption and decryption |
GPG Keys are a robust software for safe communication, and SCP gives a dependable protocol for copying them between machines. By understanding the idea of GPG keys and the way SCP works, we will be certain that our digital communications stay secure and safe.
SCP in Follow
SCP is broadly utilized in varied industries, together with finance, healthcare, and authorities. Its excessive security measures make it a really perfect selection for transferring delicate information, together with GPG keys.
For instance, within the finance business, SCP is used to switch delicate monetary information between banks and monetary establishments. The usage of SCP ensures that the information is transmitted securely, decreasing the danger of information breaches and cyber assaults.
Within the healthcare business, SCP is used to switch affected person information between hospitals and healthcare suppliers. The usage of SCP ensures that the information is transmitted securely, decreasing the danger of information breaches and making certain that sufferers’ delicate info stays confidential.
Within the authorities sector, SCP is used to switch delicate information between authorities companies and contractors. The usage of SCP ensures that the information is transmitted securely, decreasing the danger of information breaches and cyber assaults.
In every of those industries, SCP gives a safe and dependable method to switch delicate information, together with GPG keys. By understanding how SCP works, we will be certain that our digital communications stay secure and safe.
Conditions for Copying GPG Keys with SCP
Earlier than we dive into the small print of copying GPG keys with SCP, let’s first set the stage with the mandatory conditions. To get began, you may have to have a strong understanding of GPG and SSH keys, in addition to the mandatory software program and instruments to handle them.
Setting Up GPG and SSH Keys
GPG (GNU Privateness Guard) is a free and open-source implementation of the OpenPGP commonplace, which gives safe encryption and decryption companies. Then again, SSH (Safe Shell) keys are used for safe distant entry to servers and different machines. With the intention to copy GPG keys with SCP, you may have to have GPG put in in your system. SSH keys are additionally a requirement, as SCP depends on SSH for safe file transfers.
GPG and SSH keys serve totally different functions, however they complement one another effectively within the context of safe communication. GPG is used for encrypting and decrypting information, whereas SSH keys present safe authentication and authorization. Having each GPG and SSH keys arrange in your system will permit you to make the most of SCP’s options for safe file transfers.
Vital Software program and Instruments
To repeat GPG keys with SCP, you may want the next software program and instruments:
- GnuPG: That is the software program that implements the OpenPGP commonplace and gives safe encryption and decryption companies.
- OpenSSL: Whereas not strictly needed, OpenSSL is commonly used for key era and administration, in addition to for creating certificates and different cryptographic supplies.
These instruments can be utilized for a wide range of duties, together with producing and managing keys, encrypting and decrypting information, and creating safe certificates.
With GnuPG and SSH keys arrange in your system, and the mandatory software program and instruments at your disposal, you are now able to discover ways to copy GPG keys with SCP. This may permit you to securely switch recordsdata and information between machines, whereas sustaining the integrity and safety of your encrypted information.
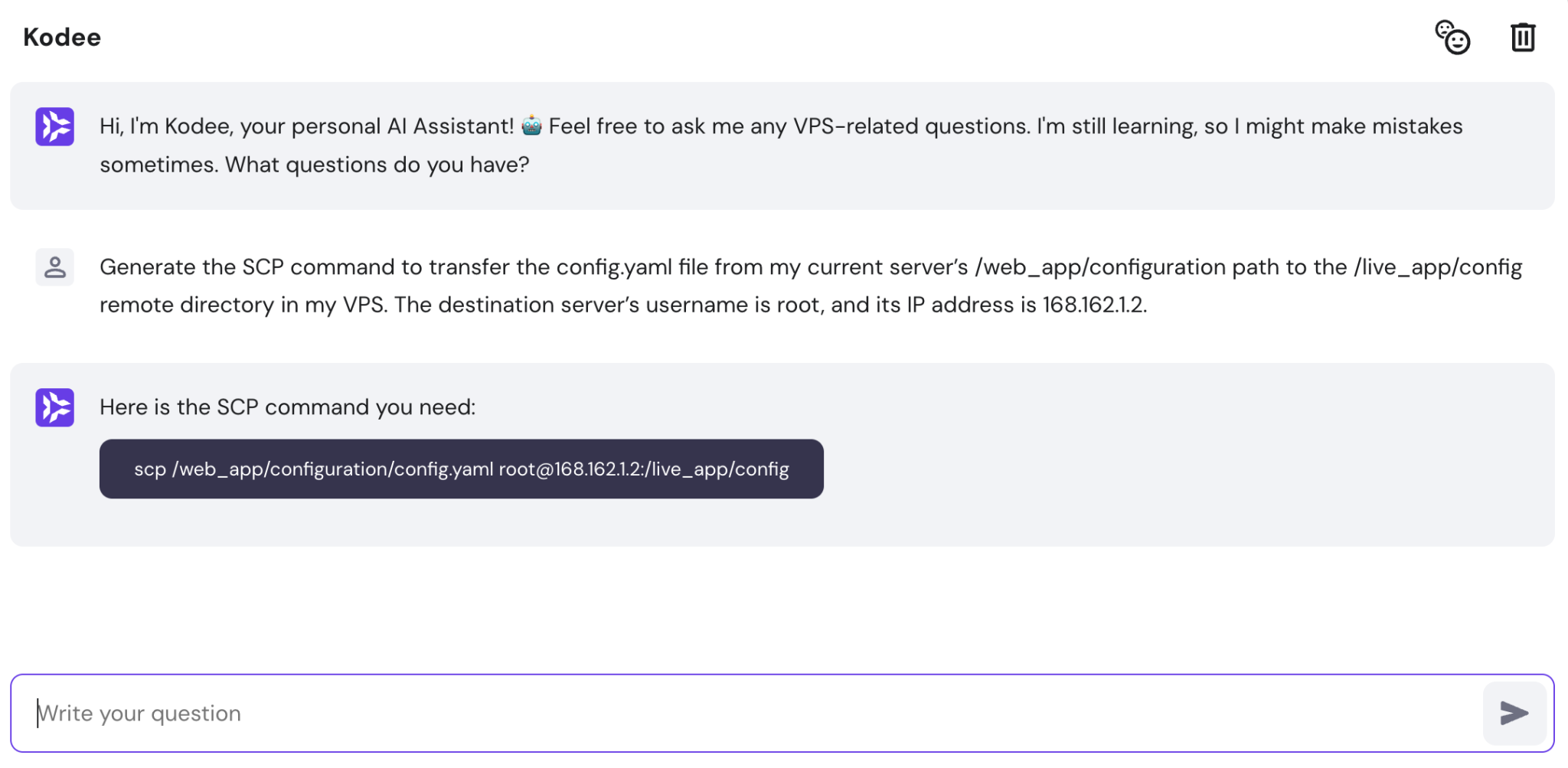
SCP’s line interface and syntax are based mostly on the rsh (distant shell) command. The overall syntax for copying a file utilizing SCP is: `scp consumer@host:/path/to/file /path/to/save/file`. This command connects to the distant host, copies the required file, and saves it to the required native path. Observe that SCP requires a safe shell (SSH) connection to be established earlier than it could provoke the file switch.
The SCP Command
The SCP command is used to repeat recordsdata securely over a community. It makes use of the SSH protocol to ascertain a safe connection to the distant host, and can be utilized for each native and distant file transfers. The SCP command syntax is as follows:
`scp [options] supply vacation spot`
Some widespread SCP choices embrace:
* `-r` for recursive copying
* `-p` for preserving file permissions
* `-P` for specifying a non-standard port
Examples of Copying GPG Keys with SCP
Listed below are just a few examples of utilizing SCP to repeat GPG keys from one machine to a different:
* To repeat a GPG key from consumer `bob` on host `192.168.1.100`, use the next command: `scp bob@192.168.1.100:/path/to/key.gpg /path/to/saved/key.gpg`
* To repeat all GPG keys from consumer `bob` on host `192.168.1.100`, use the next command: `scp -r bob@192.168.1.100:/path/to/key/ /path/to/saved/key`
SCP to repeat a GPG key (scp consumer@host1:/path/to/key.gpg /path/to/saved/key.gpg)
Configuring SCP for Safe Key Change
Earlier than copying GPG keys utilizing SCP, you may have to configure SCP to make use of a safe connection. Listed below are the steps to comply with:
1. Make sure that SSH is put in and configured on each the native and distant hosts.
2. Generate a key pair on the native host utilizing the `ssh-keygen` command.
3. Add the native host’s public key to the distant host’s authorized_keys file.
4. Check the safe connection utilizing the `ssh -v` command.
By following these steps and utilizing the SCP command, you may securely copy GPG keys between machines. Keep in mind to make use of the `-r` choice for recursive copying, and to protect file permissions with the `-p` choice.
Finish of Dialogue
![SCP Remote to Local [Practical Examples] SCP Remote to Local [Practical Examples]](https://learnubuntu.com/content/images/size/w1000/2023/09/scp-copying-folders-from-remote-to-local.png)
In conclusion, copying GPG keys from one machine to a different utilizing SCP is a vital step in safe key administration. By following the steps Artikeld on this information and adhering to greatest practices for safe GPG key administration, people can make sure the safety and integrity of their digital communications. Keep in mind, safe communication is essential to stopping information breaches and making certain the confidentiality of delicate info.
Useful Solutions
Q: What’s the SCP -line interface and syntax?
The SCP line interface and syntax differ relying on the working system and SCP consumer getting used. Nonetheless, the overall syntax for copying a file utilizing SCP is: scp [source] [destination]
Q: How do I securely retailer and handle GPG keys on a number of machines?
Use a safe key server to retailer your GPG keys and guarantee they’re encrypted. Moreover, use a password supervisor to securely retailer the passwords required to entry the keys. Lastly, use a safe protocol, similar to encrypted key storage, to switch keys between machines.
Q: Can I exploit SCP to repeat GPG keys between machines with totally different working programs?
Sure, SCP can be utilized to repeat GPG keys between machines with totally different working programs, offered that the SCP consumer is appropriate with each working programs and the GPG keys are in a appropriate format.
Q: How do I troubleshoot points with SCP key trade?
Confirm that the SCP consumer and server are appropriate, make sure the GPG keys are in a appropriate format, and double-check the syntax of the SCP command getting used.