Interactive Logon Machine Inactivity Restrict is an important facet of system safety, and it is important for customers to grasp its goal and significance. This text will delve into the world of inactivity limits, exploring its relevance, advantages, and affect on system efficiency.
The inactivity restrict is a function that robotically logs out a consumer after a specified interval of inactivity. This function is vital in varied industries, together with finance, healthcare, and authorities, the place safety and information confidentiality are paramount.
Defining Interactive Logon Machine Inactivity Restrict
The interactive logon machine inactivity restrict is an important function designed to stop unauthorized entry and make sure the safety of delicate methods. This restrict specifies the utmost interval an interactive logon machine can stay inactive earlier than it robotically locks or logs off the consumer, thereby stopping potential safety threats.
The aim of the interactive logon machine inactivity restrict is to guard delicate methods and information from unauthorized entry. By setting a time restrict, directors can scale back the chance of safety breaches, information theft, and different malicious actions that may happen when a machine stays locked and unattended.
The significance of implementing this function can’t be overstated, particularly in industries that closely depend on safety and information integrity. Industries corresponding to finance, healthcare, authorities, and protection require sturdy safety measures to safeguard their methods and information. Implementing an interactive logon machine inactivity restrict is a vital step in making certain the safety and integrity of those methods.
- Examples of Industries that Closely Depend on Interactive Logon Machine Inactivity Restrict:
Many industries depend on interactive logon machine inactivity limits to make sure the safety and integrity of their methods and information.
- Monetary Establishments
- Healthcare Organizations
- Authorities Companies
- Protection Contractors
- Manufacturing and Industrial Vegetation
Every of those industries requires a excessive degree of safety and compliance to stop information breaches and keep confidentiality. By implementing an interactive logon machine inactivity restrict, directors can make sure that delicate methods and information are protected against unauthorized entry.
Interactive logon machine inactivity limits will be set for varied varieties of methods, together with desktops, laptops, and servers. By setting a selected time restrict, directors can make sure that solely licensed customers have entry to delicate methods and information. This function is especially essential in environments the place a number of customers share a single machine or system.
By implementing an interactive logon machine inactivity restrict, directors can make sure the safety and integrity of delicate methods and information, defending in opposition to unauthorized entry, information breaches, and different potential safety threats.
Kinds of Interactive Logon Machine Inactivity Restrict
The inactivity restrict for an interactive logon machine will be configured in two alternative ways, computerized and guide, and will be based mostly on both session or idle time.
For
Computerized vs. Handbook Inactivity Restrict Settings
Computerized inactivity restrict settings enable directors to outline a selected time interval after which a consumer’s session will likely be terminated if they’re inactive. This setting is especially helpful in conditions the place directors want to make sure that customers are actively engaged on their machines. Then again, guide inactivity restrict settings present customers with the choice to reset their inactivity timer manually, permitting them to pause their session for brief intervals with out shedding their work. This function is right for customers who have to step away from their machines briefly to carry out duties not associated to their work.
Computerized settings are most popular for organizations with strict safety protocols, as they remove the potential for an idle machine getting used as some extent of assault by malicious actors. Nonetheless, guide settings are beneficial for customers who have to steadily pause their work on account of unexpected circumstances.
Computerized and guide inactivity limits additionally differ of their strategy to dealing with consumer periods. Computerized settings will be set to terminate consumer periods after a specified interval of inactivity, whereas guide settings enable customers to increase their periods or pause them when crucial.
| Inactivity Restrict Setting | Description |
| :———————— | :———- |
| Computerized | Periods are terminated after a set interval of inactivity. |
| Handbook | Customers can manually reset or prolong their inactivity timer. |
For
Session-based vs. Idle Time-based Inactivity Limits
Session-based inactivity limits are calculated from the beginning of a consumer’s session, whereas idle time-based inactivity limits are measured based mostly on the period of inactivity noticed after a consumer has logged on to their machine.
Session-based inactivity limits are sometimes most popular in environments the place customers are working for prolonged intervals, corresponding to in design, coding, or different duties that require customers to stay centered on their work. These settings are helpful in stopping customers from working in a dormant or idle state, which can point out a safety threat.
Then again, idle time-based inactivity limits will be extra versatile and permit customers to step away from their machines briefly for routine duties, corresponding to taking calls, strolling to conferences, or addressing different points unrelated to their work.
Implications of Various Inactivity Restrict Settings, Interactive logon machine inactivity restrict
Configuring the fitting sort of inactivity restrict is essential for attaining the stability between safety, productiveness, and consumer expertise.
If a company prioritizes safety over consumer comfort, it could be extra useful to configure computerized session-based inactivity limits. Nonetheless, if consumer consolation is a extra vital concern, implementing guide session-based or idle time-based inactivity limits could present customers with higher autonomy over their work periods.
The affect of inactivity restrict settings on system efficiency must also be thought of. Whereas computerized session-based inactivity limits could lead to a lower in safety breaches, they will result in a rise in logon makes an attempt as customers try and regain entry to their methods. This may occasionally trigger system load points and degrade total efficiency.
Due to this fact, directors have to fastidiously consider their group’s particular wants and necessities when configuring inactivity limits. This may occasionally contain weighing the advantages and downsides of various settings and implementing a technique that strikes a stability between safety and consumer productiveness.
Implementing and Managing Interactive Logon Machine Inactivity Restrict
Within the realm of safety and system administration, setting and managing inactivity limits for interactive logon machines is an important process. It serves as a safeguard in opposition to unauthorized entry and potential breaches. By implementing these limits, organizations can make sure that customers are periodically required to enter their credentials, thereby stopping prolonged intervals of unattended entry.
Technical Necessities for Implementing Inactivity Limits
To successfully implement inactivity limits, a number of technical necessities have to be in place. These embrace:
- An working system able to supporting group coverage or different administration instruments.
- A website or Lively Listing setup for centralized administration.
- Server software program, corresponding to Home windows Server or a appropriate different.
- Consumer-side software program or firmware that may implement inactivity limits, corresponding to Home windows Consumer.
- Community infrastructure to help safe authentication and communication.
These technical necessities allow directors to implement and handle inactivity limits successfully. The next sections will delve into the strategies for monitoring and implementing inactivity limits.
Strategies for Monitoring and Imposing Inactivity Limits
There are a number of strategies for monitoring and implementing inactivity limits on interactive logon machines. These embrace:
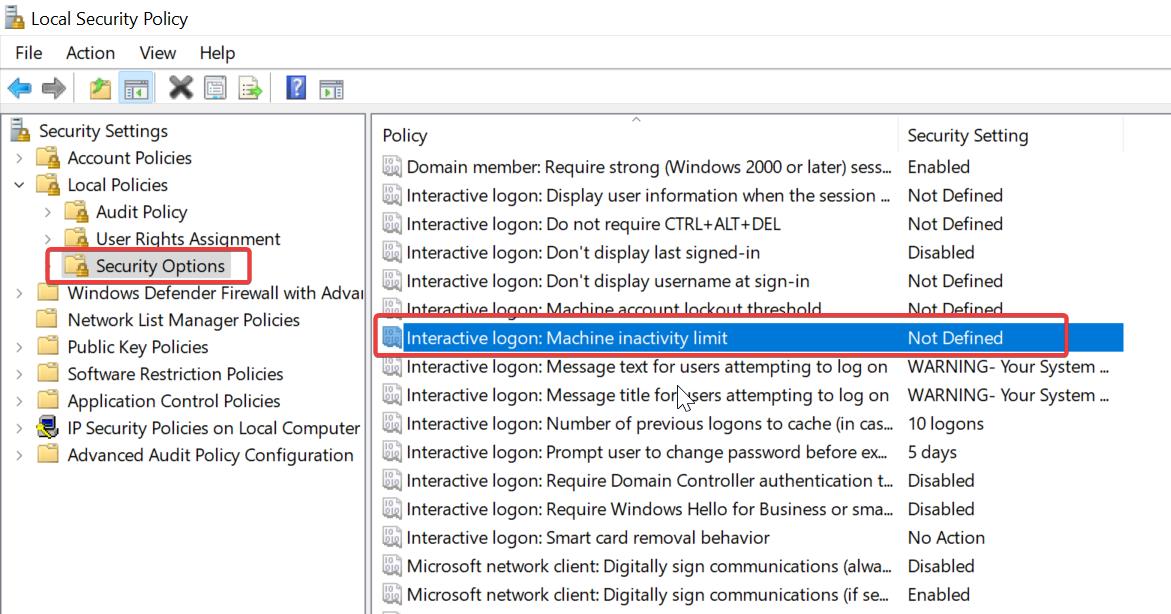
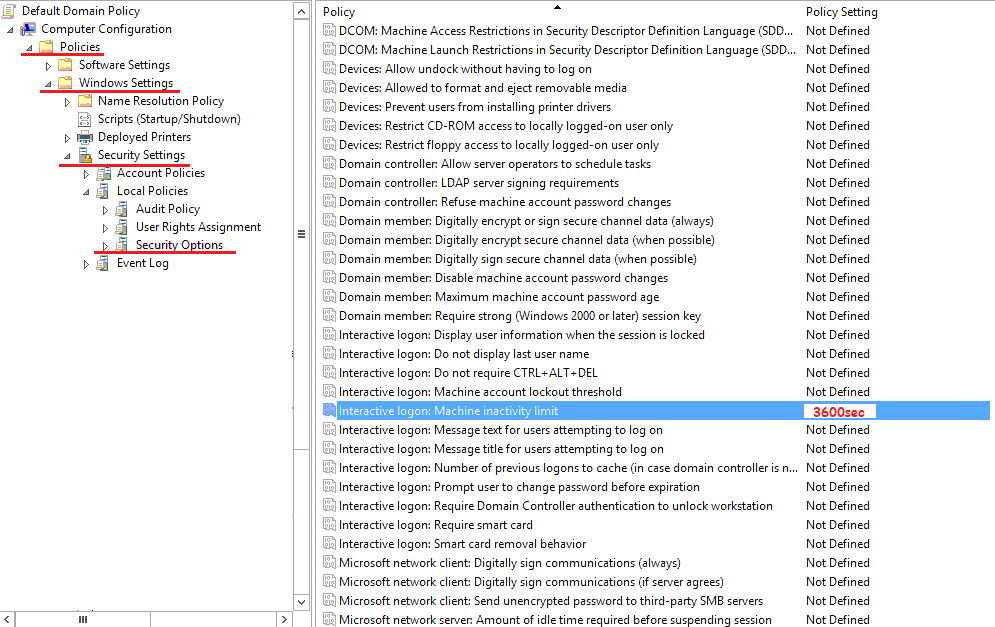
- Group Coverage Objects (GPOs): Home windows Lively Listing permits directors to create and apply Group Coverage Objects to configure settings, together with inactivity limits, throughout the community.
- PowerShell Scripts: Superior Energy Administration (APM) and Home windows PowerShell can be utilized to create scripts that implement inactivity limits and automate duties.
- Login Scripts: Native login scripts can be utilized to implement inactivity limits on particular person workstations.
- Vulnerability Scanners: Automated scanners can monitor community site visitors and detect unauthorized entry or inactivity.
These strategies present directors with a variety of choices for monitoring and implementing inactivity limits, making certain that customers adjust to safety insurance policies and minimizing the chance of unauthorized entry.
Penalties of Ignoring Inactivity Restrict Settings
Ignoring inactivity limits can have extreme penalties, together with:
- Unmanaged Entry: Unattended entry can result in unauthorized modification, deletion, or creation of delicate information, compromising community safety.
- Privilege Escalation: Inactive periods will be exploited by attackers to achieve elevated privileges and entry delicate assets.
- Information Breach: Ignoring inactivity limits can allow hackers to stay undetected, permitting them to steal delicate info or disrupt vital methods.
- Compliance Non-Adherence: Failing to implement inactivity limits can put organizations prone to non-compliance with regulatory necessities, corresponding to GDPR or HIPAA.
The results of ignoring inactivity limits are extreme and may have long-lasting repercussions, making it important for directors to prioritize the implementation and administration of those safety measures.
The significance of implementing and managing inactivity limits can’t be overstated. By doing so, organizations can considerably scale back the chance of unauthorized entry, information breaches, and privilege escalation, whereas making certain compliance with regulatory necessities.
Impression of Interactive Logon Machine Inactivity Restrict on Person Expertise
The implementation of interactive logon machine inactivity limits has been a contentious challenge in varied industries. Whereas it goals to extend safety by locking out customers who’ve been inactive for a chronic interval, it may possibly have a big affect on consumer expertise. Inactivity limits can result in frustration, lowered productiveness, and a unfavorable notion of the group or service supplier.
Results of Inactivity Limits on Person Productiveness
Implementing inactivity limits can result in a lower in consumer productiveness as a result of requirement for customers to log again in after a sure interval. This may be notably problematic for people who want to change between duties or functions steadily. For example, a consumer who’s engaged on a undertaking and receives a cellphone name could also be unable to shortly choose up the place they left off as a result of inactivity restrict, leading to misplaced time and decreased productiveness.
- Elevated time spent logging again in
- Misplaced productiveness on account of interruptions
- Decreased consumer satisfaction
In lots of instances, customers have reported feeling pissed off with inactivity limits, as they will result in a way of being “locked out” with out warning. This may be notably problematic for distant employees or people who work in areas with restricted web entry.
Different Options for Sustaining Person Engagement
Organizations can implement different options to keep up consumer engagement whereas nonetheless assembly safety necessities. Some examples embrace:
- Session timeout alerts: Informing customers when their session is about to run out, permitting them to log again in or save their work
- Auto-save performance: Robotically saving consumer information at common intervals to stop misplaced work on account of session timeouts
- Background process administration: Permitting customers to proceed working within the background whereas nonetheless assembly safety necessities
By implementing these options, organizations can stability consumer expertise with safety considerations, resulting in elevated consumer satisfaction and productiveness.
Person Suggestions on Inactivity Limits in Numerous Industries
Person suggestions on inactivity limits has been blended throughout varied industries. In some instances, customers have reported feeling pissed off with inactivity limits, whereas others have expressed help for the elevated safety measures.
| Business | Person Suggestions |
|---|---|
| Healthcare | Customers have reported feeling pissed off with inactivity limits, notably in conditions the place medical emergencies require fast entry to affected person info |
| Finance | Customers have expressed help for inactivity limits, citing elevated safety and safety in opposition to unauthorized entry |
| Training | Customers have reported feeling pissed off with inactivity limits, notably in conditions the place on-line coursework requires prolonged intervals of inactivity |
Finally, the affect of interactive logon machine inactivity limits on consumer expertise will rely on the particular wants and necessities of every group. By understanding the consequences of inactivity limits and implementing different options, organizations can stability consumer expertise with safety considerations, resulting in elevated consumer satisfaction and productiveness.
Technical Specs for Interactive Logon Machine Inactivity Restrict

When configuring interactive logon machine inactivity limits, it’s important to think about the technical specs that govern their implementation and enforcement. These specs work together with varied authentication protocols, affecting system efficiency and consumer expertise.
Interplay with Authentication Protocols
Interactive logon machine inactivity limits work together with authentication protocols by integrating with the authentication workflow. When a consumer is idle for a predetermined interval, the system triggers an authentication protocol to confirm the consumer’s credentials. This ensures that the consumer’s session stays safe and protected against unauthorized entry. For example, suppose an organization implements a 15-minute inactivity restrict for its staff’ logins. When an worker is idle for quarter-hour, the system reverts to the login display screen, prompting the worker to re-authenticate earlier than re-accessing their assets.
Enforcement of Inactivity Limits
Inactivity limits are enforced via a mixture of software program and {hardware} elements. The system periodically checks the consumer’s exercise standing, and when the restrict is exceeded, it initiates the re-authentication course of. Trendy working methods and functions make use of advanced algorithms to watch consumer exercise and regulate inactivity limits in keeping with their settings. For instance, Home windows methods use the Session Supervisor to trace consumer periods and implement inactivity limits. When a consumer is idle for an prolonged interval, the system terminates the session, prompting the consumer to log in once more.
Impression on System Sources
Imposing inactivity limits can have various results on system assets, relying on the configuration and implementation. When an inactivity restrict is exceeded, the system could provoke a re-authentication course of, which might quickly improve system useful resource utilization. This will result in a slight improve in CPU utilization, reminiscence allocation, and community site visitors. Nonetheless, fashionable methods are designed to handle these fluctuations successfully, making certain seamless consumer expertise. For example, an organization with 10,000 staff implementing a 15-minute inactivity restrict could expertise a marginal improve in system useful resource utilization throughout peak utilization hours, however this might be compensated by improved safety and lowered threat of unauthorized entry.
Troubleshooting Frequent Points with Interactive Logon Machine Inactivity Restrict
When implementing an interactive logon machine inactivity restrict, it is not unusual to come across points that may hinder productiveness and consumer expertise. This sub-section will information you thru the method of figuring out and resolving frequent errors associated to inactivity limits, in addition to evaluating approaches to error reporting and monitoring.
Figuring out Frequent Errors Associated to Inactivity Limits
Frequent errors associated to inactivity limits typically stem from misconfigured settings, consumer account restrictions, or conflicts with different system insurance policies. To troubleshoot these points, it is important to:
- Overview the inactivity restrict settings and guarantee they’re aligned with organizational insurance policies and consumer wants. For example, if the inactivity restrict is about too low, customers could expertise surprising logouts.
- Confirm consumer account privileges and permissions. Customers with restricted entry could also be restricted from configuring account settings or accessing system assets.
- Verify for conflicts with different system insurance policies, corresponding to display screen saver or password insurance policies. These insurance policies could work together with the inactivity restrict and trigger points.
- Monitor system logs and occasion viewer for errors and warnings associated to the inactivity restrict. This may assist you establish potential points and their underlying causes.
Resolving Inactivity Restrict-Associated Points
To resolve inactivity limit-related points, observe these step-by-step procedures:
- Briefly scale back or disable the inactivity restrict to check and isolate the problem.
- Restore the unique inactivity restrict setting and recreate the problem to grasp its trigger.
- Modify the inactivity restrict setting or regulate associated system insurance policies to resolve the problem.
- Confirm the adjustments and retest the inactivity restrict setting to make sure the problem is resolved.
Error Reporting and Monitoring
Efficient error reporting and monitoring are essential for figuring out and resolving inactivity limit-related points. Think about the next approaches:
- Implement a centralized logging system to gather and analyze system logs, occasion viewer entries, and consumer suggestions.
- Set up a transparent error reporting course of, together with pointers for customers to submit stories and supply related info.
- Use automated instruments to detect and alert directors to potential points associated to the inactivity restrict.
- Often evaluate and analyze error stories to establish tendencies, root causes, and areas for enchancment.
Conclusive Ideas
Summarizing the significance of Interactive Logon Machine Inactivity Restrict, it is clear that this function performs an important function in sustaining system safety and productiveness. Customers should perceive its relevance, and IT directors have to be concerned in setting the inactivity limits to make sure efficient implementation.
Important Questionnaire
Q: What are the advantages of implementing Interactive Logon Machine Inactivity Restrict?
A: The advantages embrace improved system safety, elevated productiveness, and enhanced information confidentiality.
Q: How do inactivity limits affect system efficiency?
A: Inactivity limits can enhance system efficiency by robotically logging out inactive customers, lowering the chance of unauthorized entry.
Q: Can inactivity limits be personalized?
A: Sure, inactivity limits will be personalized to satisfy the particular wants of a company or business.
Q: What are the implications of ignoring inactivity restrict settings?
A: Ignoring inactivity restrict settings can result in safety breaches, information loss, and system compromise.