With activate machine remotely on the forefront, it is a window to an incredible begin and intrigue, inviting readers to embark on a story of contemporary comfort and technological developments.
The idea of distant machine entry has grow to be more and more essential in at the moment’s world, the place machines and gadgets are being managed and monitored from afar in varied industries, together with finance, healthcare, and manufacturing.
Defining Distant Machine Entry

In at the moment’s fast-paced and interconnected world, distant machine entry has grow to be a necessary software for varied industries and people. This idea permits customers to regulate and monitor gadgets or machines from a distance, revolutionizing the best way we work and work together with know-how. The importance of distant machine entry can’t be overstated, because it improves effectivity, will increase productiveness, and enhances the general person expertise.
Distant machine entry permits customers to regulate machines or gadgets positioned in distant areas, eliminating the necessity for bodily presence and decreasing the danger of accidents or accidents. This know-how has far-reaching implications in varied industries, together with finance, healthcare, and manufacturing. In finance, for example, distant machine entry permits banks to observe and management ATM machines, guaranteeing that they’re functioning correctly and offering correct transactions.
Controlling Machines Remotely in Numerous Industries
Distant machine entry has grow to be a cornerstone in varied industries, with quite a few purposes and advantages.
Finance Business
Within the finance business, distant machine entry performs a vital position in sustaining the safety and effectivity of economic transactions. For instance, banks use distant machine entry to observe and management ATM machines, that are important to their operations.
| Business | Instance of Machine |
| Finance | ATM Machines |
| Healthcare | Medical Tools |
Healthcare Business
Within the healthcare business, distant machine entry permits medical professionals to observe and management medical gear, corresponding to ventilators or dialysis machines, from a distance. This enhances affected person care and reduces the danger of apparatus failure.
Manufacturing Business
Within the manufacturing business, distant machine entry improves the effectivity and productiveness of manufacturing traces. For example, distant machine entry permits producers to observe and management industrial robots, which carry out duties corresponding to meeting and packaging. This reduces the danger of human error and improves product high quality.
Examples of Distant Machine Entry in Motion
Some examples of distant machine entry in motion embody:
* Monitoring and controlling medical gear from a distance to make sure affected person security and luxury.
* Controlling industrial robots to enhance the effectivity and productiveness of manufacturing traces.
* Monitoring and controlling ATM machines to make sure correct transactions and preserve monetary safety.
Future Developments and Implications
As distant machine entry continues to evolve, we are able to count on to see new and revolutionary purposes of this know-how. Some potential developments embody:
* Elevated use of synthetic intelligence and machine studying to enhance the effectivity and accuracy of distant machine entry.
* Growth of distant machine entry to new industries, corresponding to transportation and logistics.
* Improvement of latest safety protocols to guard towards cyber threats and make sure the integrity of distant machine entry.
Strategies for Distant Machine Entry
Distant machine entry is an important side of contemporary computing, permitting customers to entry and management machines from anyplace on the earth. With the rising want for distant work and distributed groups, understanding the completely different strategies of distant entry is crucial for securing and sustaining connections. This part will evaluate the assorted strategies of distant entry, together with VPNs, SSH, and distant desktop software program, and talk about their benefits and downsides.
VPN (Digital Non-public Community) Connectivity
A VPN is a safe connection between two endpoints over a public community, utilizing encryption to guard information and preserve confidentiality. VPNs work by making a safe “tunnel” between the person’s machine and the distant server, successfully masking the person’s IP handle and placement. This supplies a number of benefits, together with:
- Encryption: VPNs use sturdy encryption to guard information in transit, making it troublesome for unauthorized entry or interception.
- Anonymity: By masking the person’s IP handle and placement, VPNs can present anonymity and shield person identification.
- Safety: VPNs can present extra security measures, corresponding to kill switches and DNS leak safety.
Nonetheless, VPNs even have some disadvantages, together with:
* Velocity: VPNs can decelerate web speeds as a consequence of encryption and routing overhead.
* Compatibility: Some gadgets or working programs is probably not appropriate with sure VPN protocols.
* Complexity: Establishing and managing VPNs may be advanced, particularly for giant networks.
SSH (Safe Shell) Connectivity
SSH is a safe distant entry protocol that permits customers to entry and management machines remotely, utilizing password or public key authentication. SSH works by establishing a safe connection between the person’s machine and the distant server, utilizing encryption to guard information and preserve confidentiality. This supplies a number of benefits, together with:
* Safety: SSH supplies sturdy encryption and safe authentication, making it safer than different distant entry protocols.
* Flexibility: SSH can be utilized for a variety of duties, together with file switch, shell entry, and safe tunneling.
* Customization: SSH may be personalized to go well with particular necessities, together with authentication strategies and encryption algorithms.
Nonetheless, SSH additionally has some disadvantages, together with:
* Complexity: SSH may be advanced to arrange and handle, particularly for giant networks.
* Restricted assist: SSH is probably not supported on all gadgets or working programs.
Distant Desktop Software program
Distant desktop software program permits customers to entry and management distant machines, utilizing graphical interfaces and distant desktop protocols. Some widespread distant desktop software program contains:
- TeamViewer: A well-liked distant desktop software program that gives safe, easy-to-use entry to distant machines.
- Distant Desktop Protocol (RDP): A protocol developed by Microsoft that permits customers to entry and management distant Home windows machines.
Distant desktop software program supplies a number of benefits, together with:
* Ease of use: Distant desktop software program is commonly straightforward to make use of and intuitive, making it accessible to non-technical customers.
* Flexibility: Distant desktop software program can be utilized on a variety of gadgets and working programs.
* Customization: Distant desktop software program may be personalized to go well with particular necessities, together with encryption algorithms and authentication strategies.
Nonetheless, distant desktop software program additionally has some disadvantages, together with:
* Safety dangers: Distant desktop software program can pose safety dangers, particularly if not correctly configured or secured.
* Efficiency points: Distant desktop software program may cause efficiency points, particularly if high-bandwidth purposes are used.
Greatest Practices for Implementing Distant Entry Options
To keep up safe and environment friendly distant entry options, observe these greatest practices:
- Use sturdy encryption and safe authentication strategies.
- Use safe password insurance policies and two-factor authentication.
- Implement common safety updates and patching.
- Use safe protocols and encryption algorithms.
- Monitor and audit distant entry connections.
By following these greatest practices, organizations can preserve safe and environment friendly distant entry options, guaranteeing confidentiality, integrity, and availability of knowledge.
{Hardware} and Software program Necessities
{Hardware} and software program necessities are essential for establishing dependable and safe distant machine entry. A sturdy infrastructure is important to make sure the graceful switch of knowledge and management indicators between the native and distant machines.
To facilitate distant entry, the next {hardware} elements are important:
- Community routers: These gadgets handle the circulate of knowledge between completely different networks and play a important position in establishing a connection between the native and distant machines.
- Switches: These community gadgets assist to ahead information packets between gadgets on a community, guaranteeing environment friendly communication.
- Firewalls: Firewalls act as a barrier between the native and distant networks, defending towards unauthorized entry and potential safety threats.
Along with {hardware} necessities, the next software program instruments are generally used for distant machine entry:
- TeamViewer: A distant desktop software program that permits customers to entry and management Home windows, macOS, and Linux machines remotely.
- AnyDesk: A safe distant desktop software program that allows customers to switch information, print paperwork, and entry distant machines with enhanced security measures.
| Software program Software | Description |
| TeamViewer | Distant desktop software program for Home windows, macOS, and Linux |
| AnyDesk | Safe distant desktop software program with file switch and printing capabilities |
Implementation and Configuration
To arrange distant entry on a machine, it’s important to observe a sequence of steps that guarantee a safe and useful connection. This includes configuring community settings, enabling distant entry software program, and implementing vital safety measures.
Configuring Community Settings
Configuring community settings is an important step in organising distant entry. This contains guaranteeing that the machine is correctly related to the web and that the required ports are open for distant entry. To configure community settings, observe these steps:
- Allow Wi-Fi or Ethernet connection on the machine.
- Confirm that the machine’s IP handle is assigned appropriately (DHCP or static).
- Configure the machine’s firewall settings to permit incoming connections.
- Confirm that the required ports (e.g., 22 for SSH, 3389 for RDP) are open for distant entry.
Enabling Distant Entry Software program
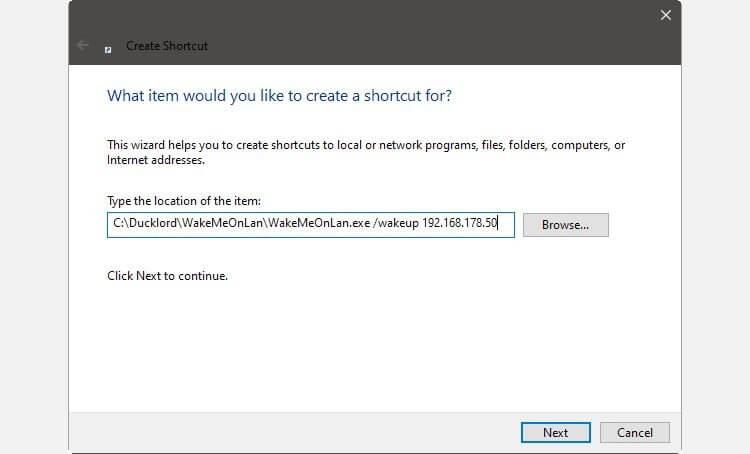
Enabling distant entry software program is one other important step in organising distant entry. This includes putting in and configuring software program corresponding to Distant Desktop Protocol (RDP), Safe Shell (SSH), or Digital Non-public Community (VPN). To allow distant entry software program, observe these steps:
- Set up RDP, SSH, or VPN software program on the machine.
- Configure the software program settings to permit distant connections.
- Confirm that the software program is correctly configured and useful.
Implementing Safety Measures
Implementing safety measures is crucial to stop unauthorized entry to the machine. This contains utilizing sturdy passwords, enabling two-factor authentication (2FA), and configuring entry controls. To implement safety measures, observe these steps:
- Set sturdy passwords for all customers.
- Allow 2FA so as to add an additional layer of safety.
- Configure entry controls to limit entry to approved customers.
- Repeatedly replace and patch the machine’s working system and software program.
Troubleshooting Frequent Points
Troubleshooting frequent points is a necessary a part of organising distant entry. This contains troubleshooting connection errors, authentication failures, and different points that will come up. To troubleshoot frequent points, observe these steps:
- Confirm that the machine is correctly related to the web.
- Confirm that the required ports are open for distant entry.
- Chech for any configuration points with the distant entry software program.
- Verify for any updates or patches for the machine’s working system and software program.
Password Administration
Password administration is a necessary side of distant entry safety. This contains utilizing sturdy passwords, enabling password rotation, and avoiding password reuse. To handle passwords successfully, observe these greatest practices:
- Use sturdy, distinctive passwords for all customers.
- Allow password rotation to make sure that passwords are modified repeatedly.
- Keep away from password reuse to stop unauthorized entry.
- Retailer passwords securely utilizing a password supervisor.
Entry Management
Entry management is a important side of distant entry safety. This contains configuring entry controls to limit entry to approved customers. To implement entry controls, observe these steps:
- Configure the distant entry software program to limit entry to approved customers.
- Use role-based entry management (RBAC) to assign customers to particular roles.
- Configure entry controls to limit entry based mostly on person location.
- Implement audit logging to observe entry and determine potential safety threats.
Safety Measures

Safety is a high precedence in the case of distant machine entry, because it immediately impacts the confidentiality, integrity, and availability of delicate information. Implementing strong safety measures is crucial to stop unauthorized entry, information breaches, and different malicious actions. A complete safety technique ought to embody encryption, authentication, and intrusion detection and prevention programs to mitigate potential dangers and threats.
Safety Dangers Related to Distant Entry
Distant machine entry will increase the assault floor, making it extra susceptible to safety breaches. Information breaches can happen via varied means, together with unauthorized entry, information theft, and interception. Furthermore, distant entry supplies an entry level for malware, viruses, and different kinds of malicious software program. It’s essential to know the potential dangers related to distant entry to develop an efficient safety technique.
-
• Information breaches can result in monetary losses, injury to status, and lack of buyer belief.
• Unauthorized entry can be utilized to control or destroy information, disrupting enterprise operations.
• Information theft can lead to mental property loss, compromising enterprise secrets and techniques.
Encryption and Safe Authentication Protocols
Encryption and safe authentication protocols are important to make sure the confidentiality and integrity of knowledge transmitted over distant connections. Encryption converts information into unreadable codecs, defending it from unauthorized entry. Safe authentication protocols, corresponding to SSL/TLS and two-factor authentication, confirm the identification of customers and be certain that information is transmitted securely.
Implementing Encryption for Information-in-Transit
Encryption is a elementary safety measure that converts information into unreadable codecs, defending it from unauthorized entry. Implementing encryption for data-in-transit is crucial to make sure confidentiality and integrity. SSL/TLS encryption protocols are broadly used to safe distant connections and shield information transmitted between programs.
Intrusion Detection and Prevention Techniques
Intrusion detection and prevention programs (IDPS) are important to detect and stop malicious actions, corresponding to hacking, malware, and denial-of-service (DoS) assaults. IDPS programs can be utilized to observe and analyze community visitors for suspicious exercise, rapidly figuring out potential safety threats.
Kinds of IDPS
There are numerous kinds of IDPS programs used to safe distant entry connections, together with:
-
• Community-based IDPS programs, which monitor community visitors for suspicious exercise.
• Host-based IDPS programs, which monitor and analyze information on particular person programs.
• Software-based IDPS programs, which monitor and analyze particular purposes.
Safety measures must be carried out at a number of ranges to offer complete safety towards varied kinds of threats.
Greatest Practices for Distant Machine Entry Safety
To make sure the safety and integrity of distant machine entry connections, organizations ought to implement the next greatest practices:
-
• Use sturdy passwords and multi-factor authentication.
• Implement encryption for data-in-transit.
• Monitor and analyze community visitors for suspicious exercise.
• Implement intrusion detection and prevention programs.
• Repeatedly replace and patch distant entry software program and programs.
Significance of Common Safety Audits
Common safety audits are important to determine potential safety vulnerabilities and weaknesses in distant machine entry connections. These audits can assist organizations develop an efficient safety technique, guaranteeing the confidentiality, integrity, and availability of delicate information.
Examples of Distant Machine Entry: Flip On Machine Remotely
Distant machine entry is an important know-how for contemporary companies, permitting workers to work from anyplace, on any machine, and at any time. On this part, we are going to discover varied situations the place distant machine entry is used, together with distant work setups, catastrophe restoration situations, and IoT gadgets.
Distant Work Setup
Distant work has grow to be more and more widespread lately, with many companies adopting versatile work preparations to enhance worker productiveness and job satisfaction. Distant machine entry permits workers to entry firm sources, collaborate with colleagues, and full duties from the consolation of their very own houses. This setup affords quite a few advantages, together with diminished commuting instances, elevated flexibility, and improved work-life stability.
- Price financial savings: Decreased overhead prices, together with workplace area and utilities.
- Elevated productiveness: Staff can work in a distraction-free surroundings, resulting in enhanced productiveness.
- Improved worker satisfaction: Versatile work preparations can result in elevated job satisfaction and diminished turnover charges.
Catastrophe Restoration State of affairs, Activate machine remotely
Catastrophe restoration requires swift and dependable entry to important programs and information. Distant machine entry permits companies to rapidly restore companies, guaranteeing minimal downtime and information loss. By having distant entry to important programs, companies can:
- Rapidly restore companies: Distant entry permits IT groups to rapidly entry important programs and restore companies.
- Reduce information loss: Distant entry permits companies to rapidly get better information, minimizing potential losses.
- Guarantee enterprise continuity: Distant machine entry permits companies to proceed working even within the face of disasters.
IoT Units
The Web of Issues (IoT) has revolutionized the best way we work together with gadgets, making it doable to remotely entry and management a variety of gadgets, from sensible house home equipment to industrial management programs. Distant machine entry permits companies to observe and management IoT gadgets remotely, bettering effectivity and decreasing prices.
- Improved effectivity: Distant entry permits companies to observe and management IoT gadgets, bettering effectivity and decreasing handbook intervention.
- Decreased prices: Distant entry can assist cut back handbook intervention, resulting in value financial savings and improved productiveness.
- Enhanced safety: Distant entry permits companies to observe and management IoT gadgets, bettering general safety and decreasing the danger of cyber threats.
Case Research
A number of industries have efficiently carried out distant machine entry, bettering productiveness, decreasing prices, and enhancing safety.
- IT and Know-how: Corporations like Amazon and Google have carried out distant work preparations, leveraging distant machine entry to enhance productiveness and job satisfaction.
- Collections and Finance: Corporations like FIS and JPMorgan Chase have carried out distant machine entry to enhance entry to important programs and information, decreasing prices and bettering productiveness.
- Healthcare: Corporations like Medtronic and Philips have carried out distant machine entry to enhance affected person care, cut back prices, and improve safety.
Remaining Evaluate
The implementation of distant machine entry presents a fancy state of affairs, the place safety issues and {hardware}/software program necessities play a pivotal position in guaranteeing uninterrupted entry and foolproof information safety.
Generally Requested Questions
What are the first benefits of activate machine remotely?
It permits customers to entry and management machines remotely, thereby rising comfort and effectivity.
Can I management any machine utilizing activate machine remotely?
No, sure gadgets or machines require particular software program or {hardware} configurations for distant entry, whereas others might have restrictions or limitations as a consequence of safety considerations.
How does activate machine remotely guarantee safety?
Implementing encryption for data-in-transit, utilizing sturdy passwords and multi-factor authentication, and monitoring and analyzing community visitors for suspicious exercise are important measures for safe distant machine entry.