Digital Machines for Linux on the forefront, we have a narrative to inform and a few data to drop, so buckle up and prepare for a journey of discovery!
With digital machines, you may run a number of working methods on a single bodily server, creating remoted environments for testing, growth, and deployment. It is like having a number of laptops in a single, however with out the muddle and expense.
Sorts of Digital Machines for Linux
Within the realm of virtualization, Linux has quite a few kinds of digital machines that cater to numerous wants and use instances. From monolithic to microkernel-based architectures, every kind has its distinctive traits and benefits.
Linux digital machines fall into two main classes: monolithic and microkernel. Monolithic digital machines, comparable to VMware and KVM, have a single, self-contained kernel that manages your entire digital machine setting.
A monolithic digital machine consists of:
- The Visitor OS (Linux on this case)
- The Host OS (the system operating the digital machine)
- The Digital Machine Monitor (VMM), which manages the visitor OS, together with the emulation of {hardware}
However, microkernel-based digital machines, comparable to Xen, have a small, light-weight kernel that handles solely important duties, delegating different obligations to domain-specific modules.
A microkernel-based digital machine consists of:
- The Microkernel
- The Area 0 (the administration area)
- The Gadget Driver Area
- The Visitor OS (Linux)
When it comes to efficiency, monolithic digital machines are typically extra environment friendly, particularly for single-VM situations. Nevertheless, microkernel-based architectures can provide higher scalability and adaptability in multi-VM environments.
Examples of digital machine architectures embody:
* VMware’s ESXi, a monolithic-type VMM
* KVM (Kernel-based Digital Machine), one other monolithic VMM
* Xen, a microkernel-based VMM
* VirtualBox, a hybrid monolithic-microkernel structure
Here’s a comparability of the efficiency of various digital machine varieties:
| Digital Machine Sort | Visitor OS Switching Time | VM Boot Time |
| — | — | — |
| VMware ESXi | 5-10 ms | 1-2 minutes |
| KVM | 3-6 ms | 30 seconds to 1 minute |
| Xen | 2-5 ms | 10-30 seconds |
Word: These values are approximate and should differ relying on the precise {hardware} and configuration.
Monolithic digital machines, comparable to VMware and KVM, are likely to have decrease visitor OS switching instances and barely longer VM boot instances in comparison with microkernel-based architectures like Xen.
Microkernel-based digital machines, comparable to Xen, have quicker visitor OS switching instances and shorter VM boot instances, making them extra appropriate for multi-VM environments.
Nevertheless, these variations might not be important in most use instances, and the selection of digital machine kind finally is determined by particular necessities and wishes.
Creating Digital Machines for Linux
Creating a brand new digital machine in Linux is a simple course of that may be achieved utilizing a wide range of instruments, every with its personal set of options and capabilities. On this part, we’ll discover the method of making a digital machine in Linux, the instruments used for this objective, and supply step-by-step directions for making a digital machine.
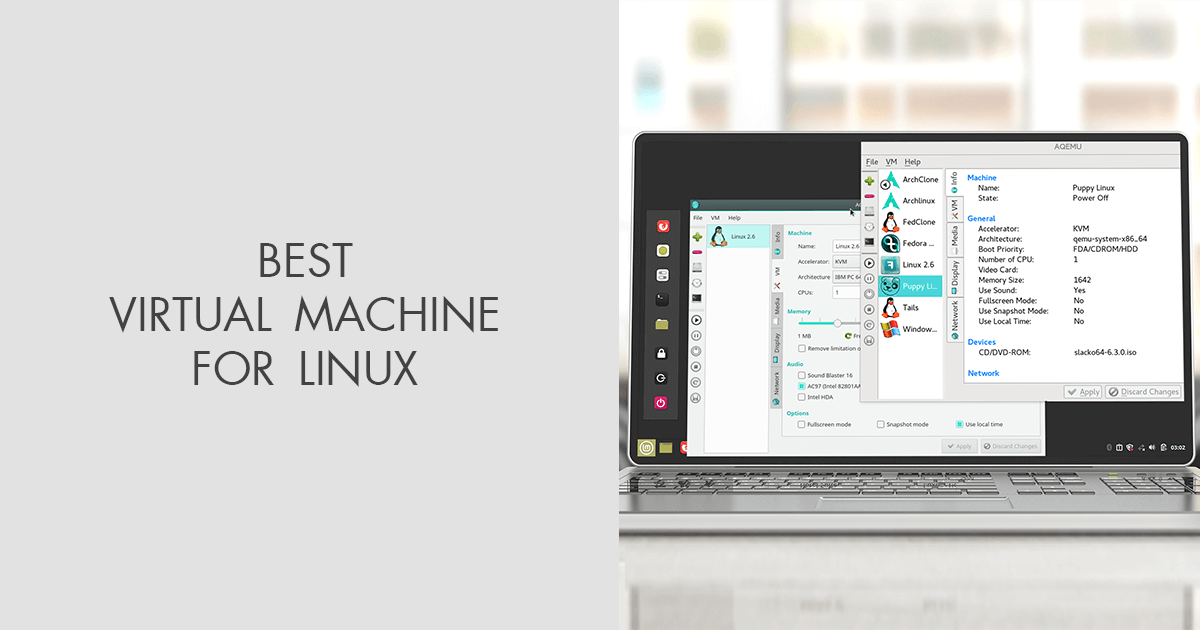
Instruments for Creating Digital Machines
There are a number of instruments obtainable for creating digital machines in Linux, every with its personal strengths and weaknesses. A number of the hottest instruments embody libvirt, VirtualBox, and KVM. Libvirt is a virtualization framework that gives a typical interface for managing digital machines, whereas VirtualBox is a virtualization software program that enables customers to create and run digital machines on a wide range of platforms. KVM, then again, is a kernel-based digital machine that enables customers to create and run digital machines immediately on the Linux kernel.
Making a Digital Machine with libvirt
libvirt is a well-liked instrument for creating and managing digital machines in Linux. To create a brand new digital machine utilizing libvirt, comply with these steps:
* Set up the libvirt bundle in your Linux system utilizing the bundle supervisor.
* Use the virsh command to create a brand new digital machine. The virsh command has a number of choices for creating a brand new digital machine, together with the `create` possibility, which creates a brand new digital machine from a disk picture, and the `import` possibility, which imports a beforehand created digital machine.
* Use the `virsh create` command to create a brand new digital machine from a disk picture. The `virsh create` command takes the disk picture file title as an argument and creates a brand new digital machine utilizing the disk picture.
virsh create Choices
The `virsh create` command has a number of choices that can be utilized to customise the creation of a brand new digital machine. A number of the most helpful choices embody:
* `-a` possibility, which specifies the disk picture file title.
* `-c` possibility, which specifies the title of the digital machine.
* `-v` possibility, which specifies the digital machine’s working system.
* `-d` possibility, which specifies the digital machine’s boot gadget.
Making a Digital Machine with VirtualBox
VirtualBox is one other fashionable instrument for creating and managing digital machines in Linux. To create a brand new digital machine utilizing VirtualBox, comply with these steps:
* Set up the VirtualBox bundle in your Linux system utilizing the bundle supervisor.
* Launch the VirtualBox utility and click on on the “New” button to create a brand new digital machine.
* Enter the title and working system of the digital machine, and choose the disk picture file from the file system.
* Configure the digital machine’s settings, together with the quantity of RAM and CPU allotted to the digital machine, and the community settings.
* Begin the digital machine and boot it from the disk picture.
VirtualBox Digital Machine Settings
VirtualBox has a number of choices for customizing the settings of a digital machine. A number of the most helpful choices embody:
* “System” part, which permits customers to specify the digital machine’s working system and boot gadget.
* “Motherboard” part, which permits customers to specify the digital machine’s CPU and reminiscence settings.
* “Arduous Disks” part, which permits customers to specify the digital machine’s disk picture file.
* “Community” part, which permits customers to specify the digital machine’s community settings.
Making a Digital Machine with KVM
KVM is a kernel-based digital machine that enables customers to create and run digital machines immediately on the Linux kernel. To create a brand new digital machine utilizing KVM, comply with these steps:
* Set up the KVM bundle in your Linux system utilizing the bundle supervisor.
* Use the `qemu-img` command to create a brand new disk picture file for the digital machine.
* Use the `qemu-system` command to create a brand new digital machine from the disk picture file. The `qemu-system` command has a number of choices for customizing the creation of a brand new digital machine, together with the `-m` possibility, which specifies the quantity of RAM allotted to the digital machine, and the `-cpu` possibility, which specifies the digital machine’s CPU settings.
KVM Digital Machine Settings
KVM has a number of choices for customizing the settings of a digital machine. A number of the most helpful choices embody:
* `-m` possibility, which specifies the quantity of RAM allotted to the digital machine.
* `-cpu` possibility, which specifies the digital machine’s CPU settings.
* `-smp` possibility, which specifies the variety of CPU cores allotted to the digital machine.
* `-device` possibility, which specifies the digital machine’s community settings.
Digital Machine Networking in Linux
Digital machine networking in Linux is essential for offering remoted networks for every digital machine (VM). This isolation ensures that VMs don’t intrude with one another’s community exercise, enhancing total system safety and efficiency.
Totally different Networking Choices for Digital Machines
Linux gives numerous networking choices for digital machines, every with its personal strengths and use instances. These choices embody Community Handle Translation (NAT), bridging, and port forwarding.
NAT (Community Handle Translation)
NAT is a networking method that enables a number of VMs to share a single IP tackle. That is achieved by translating the supply IP tackle of every packet to a special IP tackle. As an illustration, VM1 might be assigned the IP tackle 192.168.1.10, and when it sends a packet, the NAT operate interprets the supply IP tackle to the host machine’s IP tackle.
- NAT is an efficient alternative for growth and testing environments, the place a number of VMs must share a single IP tackle.
- NAT will help defend VMs from exterior assaults by hiding their IP addresses.
- NAT can result in efficiency points if not configured correctly, because it introduces a further layer of processing.
Bridging
Bridging is a technique of connecting VMs to the host machine’s community interface. This permits VMs to share the identical IP tackle because the host machine and can be utilized for servers or digital home equipment. Nevertheless, bridging requires cautious configuration to keep away from IP tackle conflicts between VMs and the host machine.
- Bridging is appropriate for server VMs or digital home equipment that require direct entry to the host machine’s community.
- Bridging might be extra advanced to arrange than NAT and requires cautious configuration to keep away from IP tackle conflicts.
Port Forwarding
Port forwarding is a technique of mapping a VM’s IP tackle and port quantity to a special IP tackle and port quantity. This permits exterior connections to be forwarded to a VM, even when the VM will not be immediately accessible from the host machine.
- Port forwarding is beneficial for purposes that require exterior connections, comparable to net servers or databases.
- Port forwarding can introduce safety dangers if not configured correctly, because it permits exterior entry to VMs.
Use of NAT, Bridging, and Port Forwarding in Actual-World Eventualities
In real-world situations, the selection of networking possibility is determined by the precise necessities of every VM. As an illustration, a growth setting may use NAT for testing functions, whereas a server VM may require bridging for direct entry to the host machine’s community. Port forwarding can be utilized in situations the place exterior connections are mandatory.
Comparability of Networking Configurations
The selection of networking configuration is determined by particular necessities, comparable to safety, efficiency, and ease of use. NAT is usually a sensible choice for growth and testing environments, whereas bridging is extra appropriate for server VMs or digital home equipment. Port forwarding ought to be used sparingly, because it introduces safety dangers if not configured correctly.
Digital Machine Safety for Linux
Digital machine safety is a prime precedence for any Linux administrator, as digital machines (VMs) can pose distinctive safety dangers. With the flexibleness to run a number of working methods and purposes on a single bodily host, VMs can even create alternatives for attackers to use vulnerabilities and achieve unauthorized entry to delicate information.
When a digital machine is compromised, your entire host system is in danger, because the attacker may doubtlessly transfer laterally throughout the community. That is why it is important to implement strong safety measures to guard digital machines and preserve the integrity of the host system.
The Safety Dangers Related to Digital Machines
Safety dangers related to digital machines in Linux embody:
- Privilege Escalation: Attackers can exploit vulnerabilities within the visitor working system or virtualization software program to achieve elevated privileges, permitting them to entry delicate information or carry out malicious actions.
- Community Exploitation: Digital machines can be utilized as a pivot level for community assaults, permitting attackers to maneuver laterally throughout the community and exploit vulnerabilities in different methods.
- Information Theft: Digital machines can be utilized to steal delicate information, comparable to encryption keys, passwords, or different confidential info.
- Malware and Ransomware: Digital machines can be utilized to unfold malware and ransomware throughout the community, inflicting important disruptions and monetary losses.
These safety dangers spotlight the significance of implementing strong safety measures to guard digital machines and preserve the integrity of the host system.
Finest Practices for Securing Digital Machines
To make sure the safety of digital machines in Linux, comply with these greatest practices:
- Use Safe Virtualization Software program: Select a good virtualization software program, comparable to VMware or KVM, that gives strong security measures, together with encryption and entry controls.
- Implement Community Segmentation: Phase the digital community to stop lateral motion and comprise malware or ransomware outbreaks.
- Use Robust Entry Controls: Implement role-based entry controls (RBAC) and be certain that all customers and directors have the minimal required privileges to carry out their duties.
- Monitor Digital Machine Exercise: Commonly monitor digital machine exercise, together with system logs, community site visitors, and disk utilization, to detect potential safety threats.
- Hold Software program Up-to-Date: Commonly replace and patch virtualization software program, visitor working methods, and purposes to stop exploitation of identified vulnerabilities.
By implementing these greatest practices, you may considerably cut back the danger of safety breaches and preserve the integrity of your digital machines and host system.
Safety Configurations for Digital Machines
To reinforce digital machine safety, configure the virtualization software program and visitor working system as follows:
- Allow Host-Solely Networking: Configure the virtualization software program to make use of host-only networking, which limits community entry to the host system and prevents lateral motion.
- Allow Encryption: Allow full-disk encryption and safe boot mechanisms to stop unauthorized entry to digital machine information.
- Configure Firewall Guidelines: Configure firewall guidelines to limit incoming and outgoing community site visitors, stopping potential safety threats.
- Implement Safe Password Insurance policies: Implement safe password insurance policies, together with password size, complexity, and expiration, to stop unauthorized entry to digital machines.
These safety configurations can considerably improve the safety of your digital machines and defend towards potential safety threats.
The Function of Entry Management in Digital Machine Safety
Entry management performs a vital function in digital machine safety, because it determines who can entry, create, modify, or delete digital machines and their related sources.
- Function-Primarily based Entry Management (RBAC): Implement RBAC to limit person entry to digital machines primarily based on their roles and privileges.
- Attribute-Primarily based Entry Management (ABAC): Implement ABAC to limit entry to digital machines primarily based on particular attributes, comparable to person ID, group ID, or file entry management lists.
- MAC (Obligatory Entry Management): Implement MAC to limit entry to digital machines primarily based on particular safety labels, guaranteeing that delicate information is protected.
By implementing strong entry controls, you may be certain that digital machines are solely accessible to approved personnel and stop potential safety breaches.
Digital Machine Finest Practices for Linux
Digital machine greatest practices for Linux guarantee environment friendly and safe utilization of digital machines in a Linux setting. Correct configuration and administration are essential for dependable and scalable digital machine operations.
Optimum Digital Machine Configuration
Optimum digital machine configuration contains allocating ample sources, comparable to CPU, reminiscence, and storage, for every digital machine primarily based on its necessities. Over- or under- allocation may end up in efficiency points or inefficient utilization of system sources.
- Assign a ample quantity of CPU sources to the digital machine, bearing in mind the workload and utility necessities.
- Allocate reminiscence sources primarily based on the reminiscence necessities of the working system and purposes operating inside the digital machine.
- Guarantee ample storage capability for the digital machine, contemplating the file system measurement and information storage necessities.
Digital Machine Backup and Catastrophe Restoration, Digital machines for linux
Common digital machine backups and catastrophe restoration plans are important for minimizing information loss and enterprise disruption in case of system failures or information corruption. Correct backup methods guarantee clean restoration and reduce downtime.
- Set up an everyday backup schedule for digital machines, together with incremental backups and full backups.
- Use a dependable backup software program that helps digital machine backups, comparable to rsync or duplicati.
- Retailer backup information on a separate bodily storage gadget or in a distant location to make sure information availability.
Troubleshooting Digital Machines
Troubleshooting digital machines entails figuring out and resolving points associated to efficiency, availability, and information integrity. Efficient troubleshooting requires a scientific strategy and experience in digital machine administration.
- Establish and isolate the difficulty: Decide the signs, scope, and root reason for the difficulty.
- Analyze and diagnose: Collect information, logs, and different related info to find out the reason for the difficulty.
- Apply fixes or patches: Resolve the difficulty by making use of fixes, patches, or updates to the working system, purposes, or digital machine configuration.
Digital Machine Documentation
Correct and up-to-date documentation of digital machines gives worthwhile info for future reference, troubleshooting, and data sharing inside the group. Correct documentation ensures environment friendly and dependable digital machine operations.
- Preserve a file of digital machine creation, configuration, and modifications.
- Doc working system and utility variations, together with software program and patch variations.
- Hold a file of backup schedules, backup information, and catastrophe restoration procedures.
Ending Remarks
We have reached the tip of our journey, however don’t fret, we have solely simply scratched the floor. Digital Machines for Linux provide a world of potentialities, and with the correct instruments and data, you may unlock its full potential.
FAQ Nook: Digital Machines For Linux
Q: What’s the distinction between virtualization and containerization? A: Virtualization creates a brand new, standalone working system for every digital machine, whereas containerization runs a number of purposes on a single working system.
Q: What are the advantages of utilizing digital machines in a Linux setting? A: Digital machines provide flexibility, scalability, and safety, making them ideally suited for growth, testing, and deployment.
Q: How do digital machines talk with the host working system? A: Digital machines use digital networking choices like NAT, bridging, and port forwarding to speak with the host working system.
Q: What are some greatest practices for securing digital machines? A: Commonly replace and patch digital machine working methods, use robust passwords, and allow entry management lists to guard towards unauthorized entry.